Malware-Plagued Pokemon GO App Making The Rounds On Android
If you haven't heard by now, Pokemon GO is taking over the world. As the most popular mobile game in recent history, the augmented reality-based app has people out searching their neighborhoods while on the hunt for Pokemon — sometimes even finding things other than Nintendo's creatures. The game is turning out to be such a big hit that its global rollout has been slowed due to overloaded servers.
In order for people in countries where the game isn't officially available yet, some users have begun sharing the app's APK files directly, giving Android users the opportunity to side-load the software and start playing early. Unfortunately, as a result, one of these APKs in circulation has been modified with malware.
The security firm Proofpoint was the first to pick up on the malicious version, noting that it surfaced within the first 72 hours of Pokemon GO's July 4th debut in New Zealand and Australia. The modified app looks almost identical to the official release, however it installs a backdoor known as DroidJack, which allows hackers to gain remote access to Android devices.
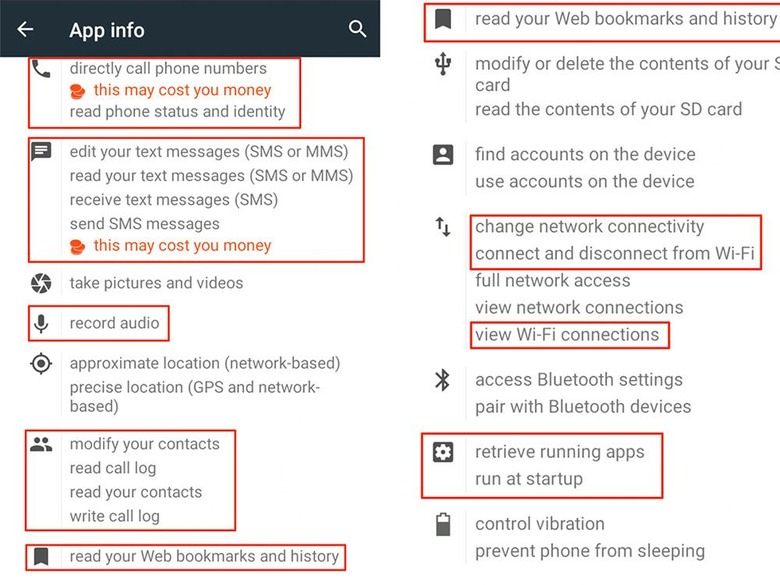
Proofpoint goes into detail on its blog about how to tell if you have the malware version of Pokemon GO installed, but the biggest warning sign is the huge list of permissions the app is granted, with some alarming things like recording audio, reading call logs and contacts, and accessing web history and bookmarks. You can find this list by navigating to Settings, Apps, and then Pokemon GO.
If you did happen to download the app's APK directly, it doesn't guarantee you have the malware version, however it increases the risk since side-loading bypasses Android's security that blocks the installation of unverified third-party apps.
In the end, this serves as a warning that it's best to just wait and get your apps from official sources, like your device's app store, even if it lets you go out and catch Pokemon in the real world.
SOURCE Proofpoint
