HTC Plans Heartbleed Fix Over Top Legacy Android Risk
Half of the top ten Android smartphones susceptible to Heartbleed hacks are made by HTC, security research firm Lookout claims, with phones like the HTC One X+ and Desire X still running older versions of Google's OS that are unpatched. Lookout describes the issues as "a curse of these phones' own success," with popular hardware unable to support the latest, safer Android versions. However, HTC tells SlashGear that it has a fix in the works.
According to Lookout, the most vulnerable version of Android is v4.1.1, which fits in with Google's own comments on the exploit. However, Lookout also spotted some 4.2.2 devices with the same issue, which it suggests may be a sign of custom OS versions being left susceptible to Heartbleed-based exploits after manufacturer tinkering.
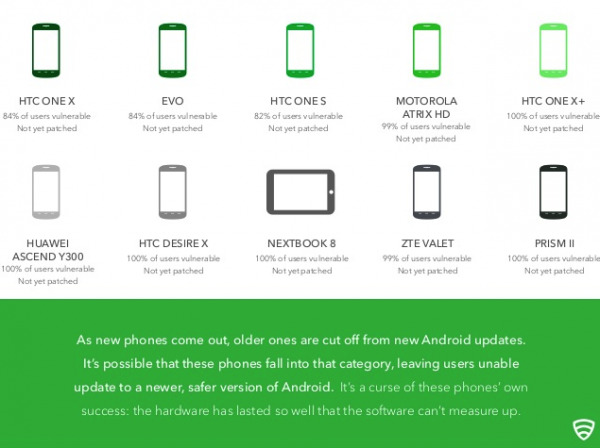
Top of the chart for most-frequently-reported Heartbleed susceptible phones are three from HTC, the research firm says. The HTC One X, HTC EVO, and HTC One S all top the charts, with Motorola's ATRIX HD taking fourth place and the HTC One X+ in fifth.
While Heartbleed's impact has been felt on Android devices around the world, Lookout says, around 3.4-percent of Android users in the US were found to be running OpenSSL versions vulnerable. That's a relatively small number, though: around 2,500 of the 75,000 US users Lookout got results from.
Although older phones like the One S and Desire X aren't likely to see a KitKat update any time soon, that doesn't mean users are being left out to dry. An HTC spokesperson gave SlashGear the following statement:
"Privacy and security are important to HTC and we are committed to helping safeguard our customers' devices and data. We're currently working to implement the security patch issued by Google this week to the small number of older devices that are on Android 4.1.1. HTC flagship devices, including the HTC One and HTC One (M8), are not impacted. As part of our normal course of business, HTC provides software updates that include security updates, which is why it is important for customers to download software updates when available."
A timescale for that security patch being pushed out has not been given.
Meanwhile, desktop users concerned about Heartbleed can patch their systems, though it's up to individual websites to update their code to address the OpenSSL liability.
