Android P Just Got One Serious Security Fix (Long Overdue)
This week we've learned of a fix to a security flaw in Android that's plagued the platform for years. The problem begins at a piece of Android called /proc/net. That's a bit of Android which currently has no restrictions for apps – they're able to read this bit of your phone's code any time they like. With this access, an app can see your TCP and UDP files, and check what you're connected to.
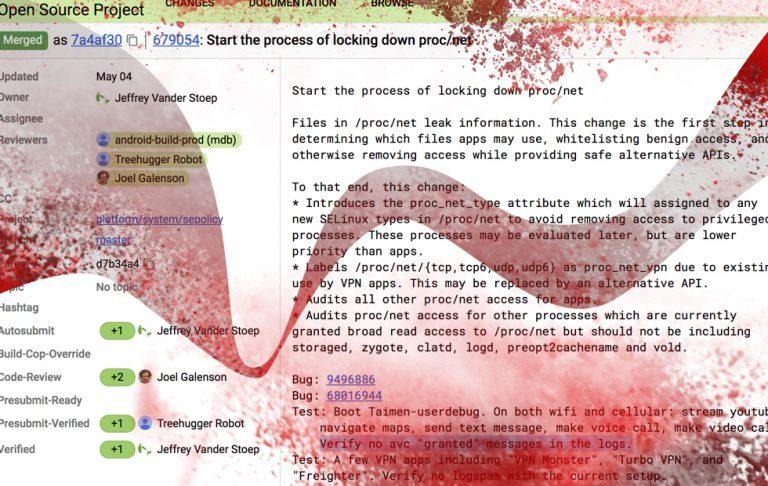
After years of this access going un-marked in AOSP, new changes are coming in effect. They've just been kicked into gear, as it were – as mentioned by XDA Developers' own Mishaal Rahman. As Rahman mentions, a new commit appeared this week in AOSP which tips the start of "the process of locking down proc/net" at long last.
SEE TOO: View and control your Android from your PC: here's how"
In the change in AOSP (on GoogleSource numbered 679054, it's mentioned that "Files in /proc/net leak information. This change is the first step in determining which files apps may use, whitelisting benign access, and otherwise removing access while providing safe alternative APIs." This test and commit was first submitted by developer JV Stoep and reviewed by Treehugger Robot, J Galenson, and Android-Build-Prod (MDB).
This commit aimed to audit /proc/net access for processes given access they very well should not have had. That's processes gaining read access to /proc/net including storaged, zygote, clatd, logd, preopt2cachename, and vold. Such nonsense. Such fixes needed.
It would currently appear that this change – and/or set of changes – is coming to API level 28 running on Android P. That means it won't necessarily come to older phones – which is sort of a bummer, but not entirely unexpected. Unlike a foolish past version of myself, I now understand: you need that new software so the bad hackers can't come get you.
There's nothing most users can do right this minute to bring about this fix – unless they're all about that custom ROM use. Everyone else is going to need to wait for the next couple of Android P updates – coming sooner than later. Keep a weather eye.