Razer Data Breach Indexed By Search Engines
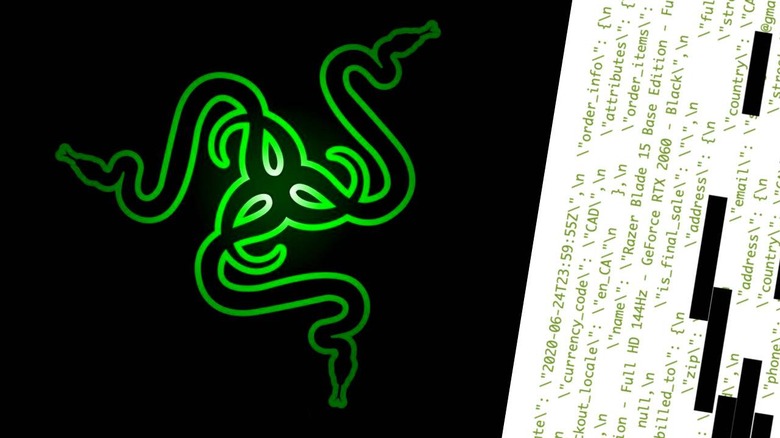
A data breach surfaced this week showing personal identifiable information for Razer product consumers. Information appeared in a leaked Elastisearch data cluster – something that should never, ever be public, in this case. In the data leaked, Razer customer purchases, email, physical address, phone number, and more were exposed. Per the report, this data wasn't just readable, it was indexed by public search engines!
The good news here is the key elements that were not exposed. No credit card numbers were exposed, and no passwords were exposed. Of course, that's beside the point – if the point is that personal information of any sort shouldn't be available to the public at any point, no matter what.
If you've purchased a Razer product at any point in the past, and you receive an email or telephone call about said purchase, you'll do well to keep an eye out for fraud. Never provide information of any sort to cold calls or emails requesting information that you wouldn't provide a stranger.
You'll find additional information in the main report from security researcher Volodymyr "Bob" Diachenko on LinkedIn (of all places) right this minute. This case has been in the works for some weeks, at least – and it's not over yet! Per Diachenko "the exact number of affected customers is yet to be assessed as originally it was part of a large log chunk stored on a company's Elasticsearch cluster misconfigured for public access since August 18th, 2020 and indexed by public search engines."
Per the post from ArsTechnica, Razer offered the following note on the subject: "We were made aware by Mr. Volodymyr of a server misconfiguration that potentially exposed order details, customer and shipping information. No other sensitive data such as credit card numbers or passwords was exposed."
Razer went on to note that the "server misconfiguration" was fixed on the 9th of September, 2020, "prior to the lapse being made public." Razer has an email address available for customers that have concerns about the situation at DPO@razer.com. Let us know if this breach has affected you, and we'll continue to investigate!