No Permissions Android App Shows Three Giant Security Loopholes
The Leviathan Security Group have released a proof of concept application for Android which shows three ways an application can readily scan and use your data without any permissions granted to it. As all Android users know, whenever you download an app from the Google Play App Store, you've got to tap through a screen which asks you if it's alright that an app has certain permissions to access your phone or tablet's abilities. The app you're about to witness has no permissions necessary to click through, yet it does have the ability to bypass your device's security – unsettling, yes?
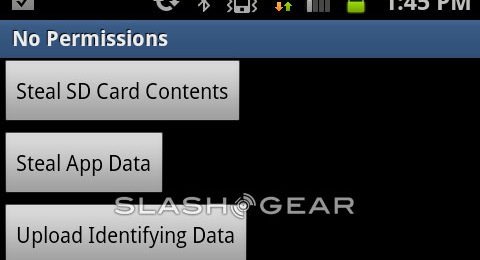
What you're seeing above is all the app really consists of on the visual end. The three permissions this app has that are not included in Google's App Store requirements for an OK by you are these: SD Card Contents, App Data, and the ability to upload this content to a third party server. In the app itself, you've got to tap a button to make these actions occur, of course, but each of these abilities could very well be built-in without a users knowledge and deployed automatically once the application is downloaded to your device.

The SD Card can be read, first of all, by any app without your permission – here lies all the app data your apps have decided to keep there, unprotected. Also here are your photos and videos as well as some external configuration files – Leviathan even found their OpenVPN certificates in this space for easy consumption.
Your data/system/packages.list file can be access by this app, no permissions needed. This list shows what apps are on your device and where they are, this allowing the app to then potentially seek out and read all files that are publicly available in app directories across the board. This app can also grab identifiable information about the device itself including GSM and SIM vendor IDs, kernel, ROM, and the Android ID – a 64-bit number randomly generated the first time the device is booted, sticking to the device forevermore.
The last button then should be rather obvious, transmitting this data to the web whenever the device has access to the internet. The URI ACTION_VIEW Intent network call can by activated by any app without your permission – GET parameters can then be used to pass data to whatever location the app calls for.
You can grab the source code as well as the APK file for this app from Leviathan Security if you wish to fiddle around with them. Meanwhile hope that these holes are blocked up in one way or another soon!
[via Leviathan Security]