iPhone APIs Allow Data Harvesting On Unmodded Handsets Warns Developer
iPhone security is a hot topic, and so when a developer takes to the stage to describe how rogue applications could "harvest personal data" on an unmodified iPhone without a user realising, you know there's going to be some coverage. Nicolas Seriot gave a talk about iPhone Privacy in Geneva this week, and listed several ways [pdf link] in which Apple's own APIs could be used to read or edit the address book, browse Safari and YouTube history, recent GPS position and more.
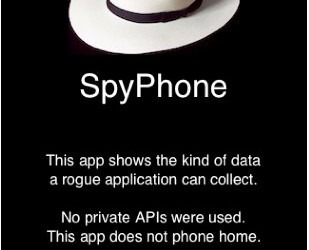
Seriot has put together an app – SpyPhone – that demonstrates what data is available merely through the standard APIs, and at first glance it's eye-watering stuff. While passwords are blanked out, there's a keyboard cache that logs every other word typed on the iPhone (it's used in autocompletion). However, as the commenters at Slashdot have been discussing, security on the Apple smartphone is not just a case of on-device safeguards.
Instead, Apple's own approval process should be enough to weed out any potential malware misusing these public APIs. One comment points out that Apple are now paying extra attention to strings that access preference and temporary files, and would be unlikely to allow through anything that looked suspicious. However, there's certainly a case – as another comment suggests – for Apple introducing more stringent user warnings, similar to those on Android, which would inform users what capabilities a newly downloaded app has in terms of accessing other areas of the system. Nonetheless, that information is only as useful as the smartphone owner makes it; there'd need to be some sort of eduction process too, else people would likely just hit "OK" without really paying attention.
[via Slashdot]