Flappy Bird Clones Add Costly Malware Risk Warn Experts
Flappy Bird's creator may have yanked the game out of concern for players' addiction to the hit title, but fake versions may do damage to their wallets instead, with trojan malware flooding the Google Play store. Beleaguered developer Dong Nguyen opted to pull the official downloads of Flappy Bird because the thought of players unable to put down the simple game was giving him sleepless nights. However, its absence opened the gates for clones to take its place, some of which have been found to make unexpected premium charges to monthly smartphone bills.
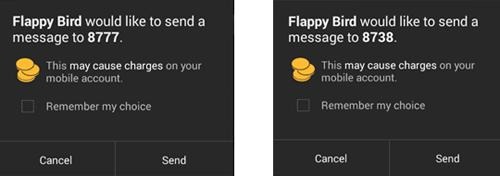
Several Android clones have been found to send messages to premium numbers, resulting in potentially high fees being billed to the user's cellphone account. Unlike the original Flappy Bird, the lookalike apps request text message permissions during installation, Trend Micro observed, and then begins attempting to send messages to premium numbers.
Although those attempts result in a pop-up warning, requiring permission from the user, that's not the only malware action going on. While it's running, the fake game also connects to a remote server for instructions on how to send messages and hide notifications of incoming messages "with certain content" the security researchers found.
In addition to direct charges, the exploit also opens the user up to future phishing attempts, as it also reports the device's telephone number, carrier, and Gmail address to the malware C&C server.
According to Trend Micro, the apps are most commonly being seen in Russia and Vietnam, though it's likely that they could spread to other countries. Given that the reply messages are hidden, it's entirely possible that users affected would only discover they'd been the victim of a scam when the monthly statement from their carrier arrived.
Luckily, safer alternatives for those who didn't download the original game when it was available are still around; we've pulled together some of the best examples here, including ways to play Flappy Bird on your Pebble smartwatch. Sideloading to an Android handset or a jailbroken iOS device is also an option, if you have the original install file, but does open the door to the possibility of inadvertently loading malware if you're not careful about where you source that file from.