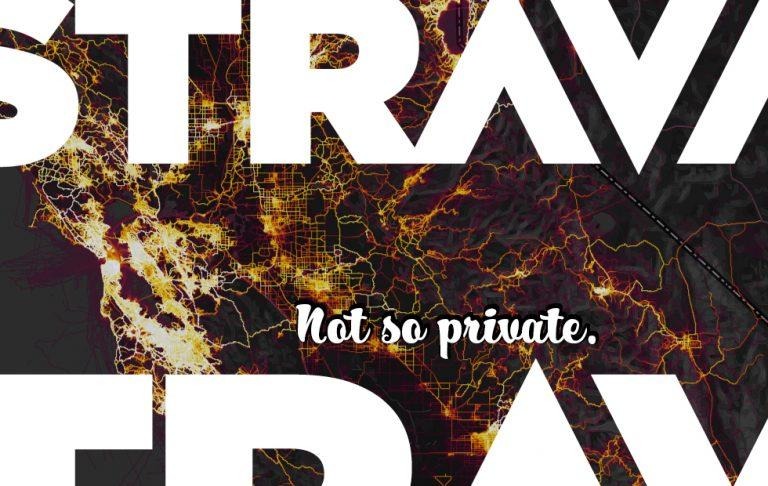
Fitness Tracker Strava Reveals Names, Locations, Heart Rates
I'm currently looking at heatmaps showing the exercise paths of soldiers on live military bases around the world. I'm able to do this thanks to the fitness social network Strava. Much like a soldier sharing photos of their base on Facebook, Strava shows the paths they run on every day. Strava shows this information because these soldiers shared this information with Strava, and therein potentially enemy forces, too.
Earlier this week my colleague Chris Davies published an article called Do you want a private Android phone or a useful one? The situation with Strava is much in the same vein. If you want useful information from Strava on your run, you've got to give Strava your run info. Unfortunately Strava's not keeping that info particularly secret from those that might seek it with malicious intent.
Christopher Miller, Ukraine-based correspondent covering the former Soviet Union for @RFERL & @pressfreedom, created a timeline of heatmaps he discovered with Strava's developer API requests. These heatmaps we reported on in part this morning are not private.
The only people to have access to ruined Donetsk airport these days are Russian & separatist military types. Strava data appears to show their operating area & most-traveled paths to & from key locations. pic.twitter.com/qXjih5BoSD
— Christopher Miller (@ChristopherJM) January 29, 2018
One can make a request of Strava's developer API for any specific location in the world. When a location is requested, the fitness data in the area is shared, including names, routes of runs, heart rates, and running speeds. Again, this information is not private, nor is it protected in any serious way.
Washington Post Beirut bureau chief Liz Sly on Twitter reported that a spokesperson for US Central Command spoke up on the matter this morning. "The rapid development of new and innovative information technologies enhances the quality of our lives but also poses potential challenges to operational security and force protection."
"We constantly refine policies and procedures to address such challenges." said Central Command. "The Coalition is in the process of implementing refined guidance on privacy settings for wireless technologies and applications, and such technologies are forbidden at certain Coalition sites and during certain activities. We will not divulge specific tactics, techniques & procedures. However, we have confidence in our commanders' abilities to enforce established policies that enhance force protection & operational security with the least impact to our personnel."
The worldwide mega-addiction to social networking and sharing of every element in one's own life is bound to be the downfall of us all. Unless we reign it in. Let us know if you're all about it, or if you've made the move to cut yourself off entirely.