Equifax Data Breach: The Shocking Security Just Got Worse
Another Equifax portal was found to be negligent in keeping up with security protocol this week. This portal was discovered by Hold Security LLC, which found a new online portal for Equifax employees to manage credit report disputes (with personal info inside). This portal was guarded only by a single name/password digital doorway whose name and password were both "admin".
The portal's name was Veraz (Spanish for truth or truthful), and it's been taken offline as of last night. This was only after Equifax was told about the potential security breach by KrebsOnSecurity, informed in turn by Hold Security LLC. Inside the page, a list of active and inactive Equifax employees was found inside, along with contact information.
While guessing Admin/Admin was easy enough, this page also revealed that each employee login was also super simple. All names and passwords were stored on this webpage in plaintext in the page's HTML. But it's not as if any of these names and passwords were difficult to guess – every name and password was an employees last name for login and... the employees last name again for password.
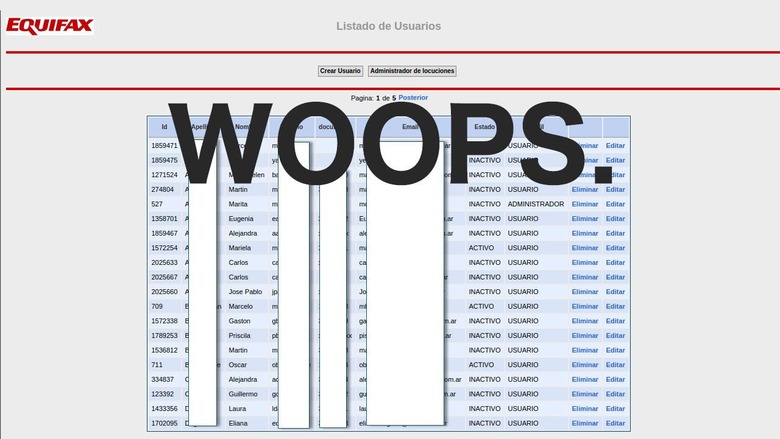
This is only the top level – the login is the easy part. It's precisely the part of this setup that should be the most difficult to parse. But Equifax's site here in Argentina was early-1990's-level simple to break into. Inside the portal was a massive stockpile of Equifax user information.
Included on the list were the following:
• Name
• DNI (Argentinian version of Social Security Number)
• Complaint and/or Resolution
KrebsOnSecurity reported that this portal contained "750 pages worth of consumer complaints — more than 14,000 in all". And this isn't likely the end of this tale of terrible security and information leaks from Equifax. Have a peek at our Equifax security breach 2017: The Fine Print guide to learn more about what you can do to protect yourself – and see if you're already potentially a victim.