China Allegedly Using iCloud To Spy On Its Own Citizens
While Apple fans, both around the globe and in China, might be celebrating the availability of the new iPhone 6 and iPhone 6 Plus smartphones in the country, they should probably start rethinking their merry thoughts, depending on their beliefs on how much the government should be able to access about their personal lives. A report is now surfacing that the Chinese regime is using its famous (or infamous) "Great Firewall of China" to compromise the security and privacy of iCloud users using an age-old man-in -the-middle attack.
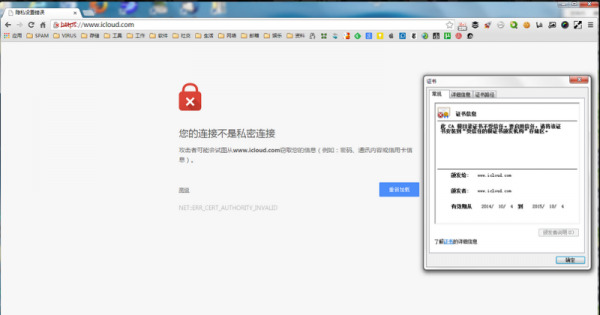
This type of attack, abbreviated to MITM, is one where a third party eavesdrops on communication by establishing a connection between two points and relaying the messages between the two. The crucial point is that neither party would normally be able to tell that there is anything wrong with the connection as the messages are conveyed without problems when, in fact, a third party is also privy to everything that goes in between. The government uses a fake security certificate to make it seem that browsers and devices are connecting securely to iCloud. By using this connection, the government is able to access any data that goes from user to server and back, including iCloud usernames and passwords, which the government can then potentially use to retrieve data from iCloud backups.
That the Chinese government would spy on its own people or use the Internet to do so is definitely nothing new. What's new here is that it involves Apple, who is just beginning to make inroads in the large Chinese market. The Cupertino-based company has just recently boosted the security and privacy features of its devices and services, supposedly in response to the US government's own revealed spying activities. Ironically, that same hardened security might have led the Chinese government to resort to this MITM measure while allowing the sale of the device in the country.
Unlike the scandal that rocked iCloud in the US, this problem can hardly be blamed on Apple, though it can perhaps be questioned about how willing it is to do business with someone who can easily besmirch its name. Given how Apple product users are intimately tied to iCloud, there is very little escape from this problem. Those accessing the service via browsers are advised to use browsers that are able to detect such attacks, such as Firefox or Chrome. That, however, doesn't really give much of an option to those using Safari or built-in browsers. Such users can also resort to VPNs, though it is not something a regular user might be accustomed to. And as a last resort, users should also enable two-step authentication to prevent unauthorized access, even if the Chinese goverment already has access to login credentials.
SOURCE: GreatFire
VIA: Ars Technica