Certifi-Gate Uses Android Remote Support Tools To Cause Harm
Just when you thought the nightmare might soon be over, another Android security vulnerability comes along to ruin your day. Fortunately, as scary as the name might sound, the Certifi-gate bug isn't as easy to catch, as it does require a certain number of factors to be in place. That said, given how users are quite prone to what is termed as "social engineering", or getting them to do things they shouldn't under normal circumstances, it might actually not be that hard to pull off.
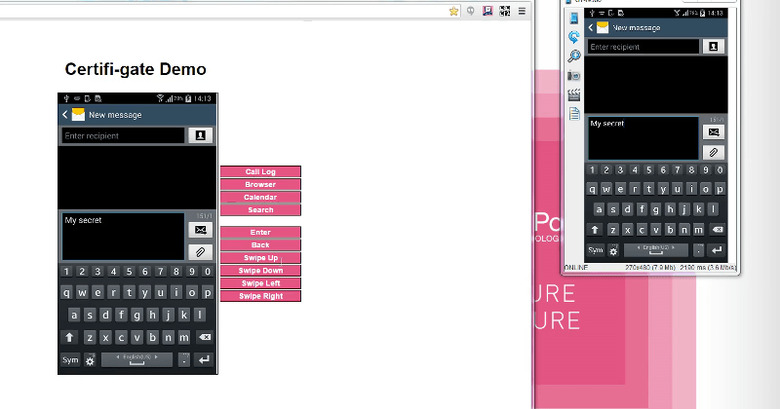
At the heart of the problem lies Android's support for mobile Remote Support Tools or mRSTs. That might sound alien, but they are also known in more popular forms as things like Team Viewer or remote desktop control. In practice, these tools allow customer support representatives to remotely and temporarily take control of a user's device, either to show them how to do something or to fix a problem.
While that is good in theory, according to Check Point's mobile threat research team, the Android implementation unfortunately comes short of being foolproof. Malicious individuals (a.k.a. hackers) can masquerade as legitimate support tools or personnel and take control of a device. If that weren't bad enough, they can even gain privileges to access data or actions that are normally out of reach from legitimate support representatives.
Given that mRSTs are popular and convenient ways to do user support, they are widespread among devices, both as official manufacturer or carrier tools and as third party alternatives like TeamViewer. That makes Certifi-gate a wide-reaching vulnerability that is also difficult to actually fix. Or to be exact, being part of a device's firmware, it's even harder to roll out the fixes in a timely manner.
Hopefully, Stagefright has scared enough vendors to actually make that a thing of the past. Google, Samsung, and LG have all publicly committed to a monthly update cycle for security fixes, which could cover this Certifi-gate exploit. Whether they manage to pull that off is another story.
SOURCE: Check Point