Behind "The Mask": Huge, Sophisticated "Careto" Malware Discovered
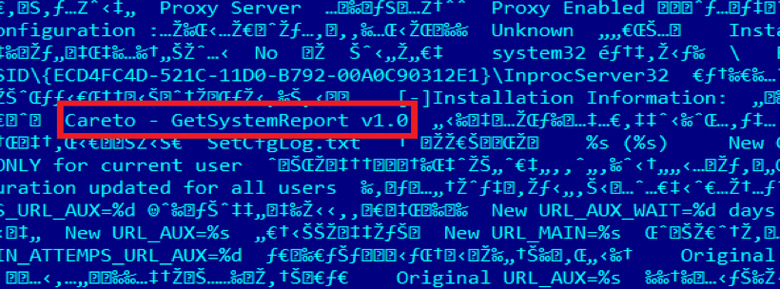
What could be one of the most advanced cyber-espionage and malware systems has been identified, with Kaspersky Lab discovering a wide-reaching hacking scheme that has affected more than 380 different victims across 31 different countries. Dubbed "The Mask" from the Spanish slang "Careto" – meaning "ugly face" or "mask" – found in the malware code, the hackers have put together what Kaspersky describes as an "extremely sophisticated" set of tools including versions for Windows, Mac, Linux, and potentially Android and iOS. In addition to the broad range of potential victims, the amount of data that can be extracted from an infected machine is vast.
For instance, a compromised system can have all network traffic, any keystrokes made, all Skype conversations, and any PGP security keys reported back to "The Mask" operations. It's also capable of analyzing WiFi traffic, sucking out all the data from Nokia devices, making screen captures, and tracking all file operations.
In fact, despite considerable investigation by the security team, several aspects of the toolkit are still not understood fully. Some are monitoring unidentified extensions that Kaspersky theorizes could be related to military and/or government encryption.
Infections themselves are usually by a phishing email, which links to malicious files stored on one of a number of exploit websites. Signed with a valid security certificate to increase the chance of being mistaken for legitimate, the malware then opens a range of backdoors and begin funneling out information.
Kaspersky Lab first noticed "The Mask" operations when it became clear the malware was trying to exploit an old version of the company's security software, so as to make itself effectively invisible to scans. When the team dug through the evidence, it realized that the malware had in fact been active for more than five years, and was effectively more sophisticated than previously identified threats like Duqu, Gauss, RedOctober, or Icefog.
Many of the domains used to infect victims have now been shut down, and in fact the team running "The Mask" ceased operations last week after some details of the exploit were made public. However, it's suggested that resuming it would be a trivial thing, while the absence of evidence to pick out specific iOS and Android backdoors possibly meaning mobile devices are still particularly at risk.
VIA Threatpost