2.27m Users Installed Malware With Tainted CCleaner Download
In the grand annuls of software irony, apps that explicitly promise to make your computer more stable being used to secretly distribute malware are top of the list, especially when they happen to be owned by anti-virus specialists. It's a cluster of coincidences that makes news that CCleaner, the free system tune-up tool offered by Avast, was unwittingly used to load a backdoor in users' PCs. During the period it was compromised, 2.27m people installed the infected app.
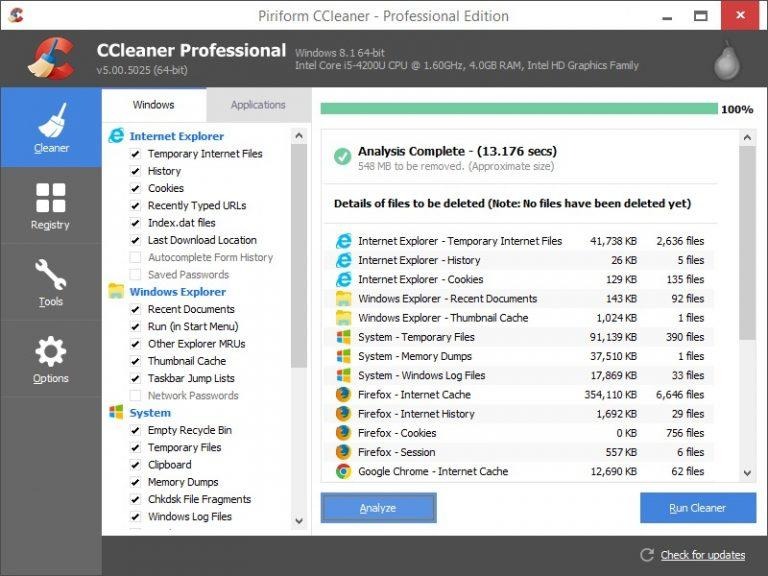
CCleaner began as an independent project by developers Piriform all the way back in 2003, as a way to remove unnecessary data such as temporary internet files and erroneous Windows registry entries. The app could also clear out file fragments, delete unneeded logs, and remove programs that have hooked into the Windows startup and thus load automatically each time the PC is booted. In July of this year, Piriform was acquired by Avast.
Come September 13, Cisco's Talos Intelligence spotted something strange. While conducting beta tests with consumers of its latest exploit detection technology, it identified that the installer for CCleaner v5.33 was triggering an alert. Users had been downloading the file from the legitimate CCleaner download servers, Talos says.
The problem, it turned out, was that the CCleaner download was being coopted by a malicious payload. While the official app was signed using a valid digital signature issued to Piriform, Talos says, the 32-bit CCleaner binary "also contained a malicious payload that featured a Domain Generation Algorithm (DGA) as well as hardcoded Command and Control (C2) functionality." With that tool installed, the PC communicates with a remote server to report that it has been compromised.
CCleaner 5.33 has been removed from the official servers, and is no longer available to download. However, it was the preferred version of the app between August 15 and September 11 of this year, after which point it was replaced by CCleaner 5.34 which did not suffer the same infection. According to Avast, 2.27m people downloaded the file in that time.
The advice now is to restore any potentially infected systems to a state prior to August 15, or to reinstall them. Anybody with CCleaner installed should update to the latest version, which in many cases will be a manual process.
"This is a prime example of the extent that attackers are willing to go through in their attempt to distribute malware to organizations and individuals around the world," Talos concludes. "By exploiting the trust relationship between software vendors and the users of their software, attackers can benefit from users' inherent trust in the files and web servers used to distribute updates."
As for Piriform, Paul Yung, its VP of product, apologized for the security lapse though downplayed its severity. Writing on the company's official blog, he argues that "the threat has now been resolved in the sense that the rogue server is down, other potential servers are out of the control of the attacker, and we're moving all existing CCleaner v5.33.6162 users to the latest version. Users of CCleaner Cloud version 1.07.3191 have received an automatic update."