SLAM Method: What It Stands For (And How It Can Save You From Hackers)
The internet became a thing just over four decades ago, and has now transformed into an essential service that connects billions of people worldwide. Every major industry, including healthcare, banking, and entertainment, relies heavily on digital communication. As convenient as instant access to millions of websites and apps has become, it has also opened the door for bad actors that find vulnerabilities to exploit users' personal information. According to the U.S. Department of State, cyber criminals caused over $4 billion worth of financial losses in 2020 alone.
Top-rated antivirus programs like Norton and McAfee protect against various kinds of malware, which are usually beyond the control of the user once the malicious files have made their way into the system. Despite the clever advancements in the delivery mechanisms and execution strategies of malware, phishing remains a widely adopted method among cyber criminals. This is largely thanks to phishing being an easy yet persistent form of social engineering — often with a high success rate.
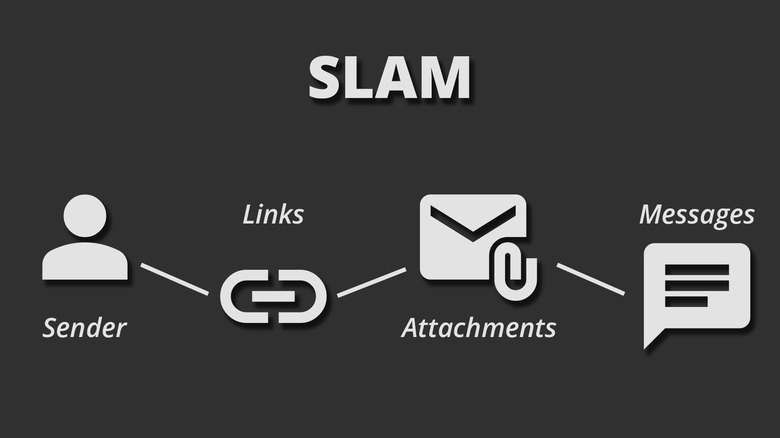
With phishing, cyber criminals send fraudulent emails or messages to users, and these victims, who often don't know any better, end up clicking on malicious links or downloading attachments. An effective defense against falling victim to phishing attacks is adopting the SLAM method. It's a quick, four-step checklist that encourages users to briefly pause and examine potentially dangerous emails or text messages. It's an acronym that stands for Sender, Links, Attachments, and Messages — four variables to look out for in any new emails.
Using the SLAM method
The SLAM method advises all internet users to check for the following four key aspects in any suspicious emails or messages they receive:
- Sender: Carefully examine the sender's email address or phone number, in the case of a text message. Look for spelling errors or cleverly masked domains. For example, an email from "xyz@apple.com" is legit, whereas one from "xyz@apple-support.com" should raise immediate suspicion.
- Links: Many phishing attacks depend on the victim clicking on fraudulent links. Before you click on a link in an email, hover your cursor over it to preview the URL. Most browsers show the destination URL at the bottom of the screen, and you can also long-press on a mobile to view a preview of the webpage. This can help you identify scam websites that disguise themselves as legitimate login portals.
- Attachments: Only download attachments from trusted senders. With document-based malware, PDFs or Microsoft Office files are laced with malicious macros that execute when they are launched.
- Messages: Sometimes carefully going through the contents of an email or a text message is enough to spot an attempted phishing attack. Look for inconsistencies in the font and color, in addition to poor grammar or spelling mistakes.
It only takes a few intentional applications of using the SLAM method before it develops into habitual instinct. Not to mention, it's a fast and effective measure against phishing attacks that doesn't require any fancy apps or browser extensions.
What to do if you receive a phishing email
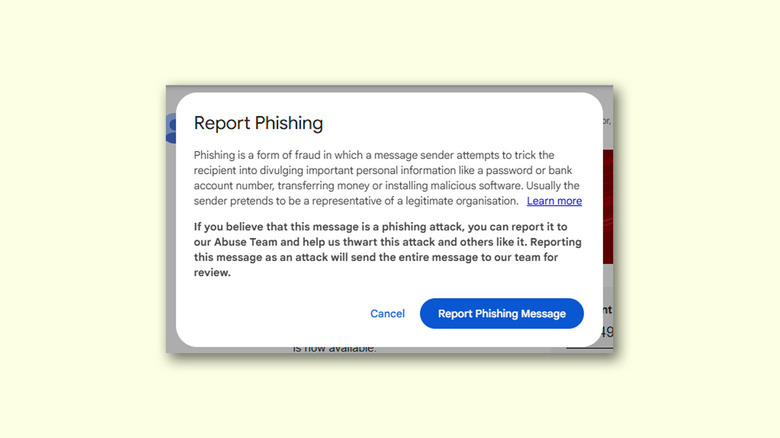
The safest way to deal with a phishing email is by not interacting with any links or attachments it contains. If, after a quick SLAM analysis, you determine that an email you've received is potentially fraudulent, you should delete it. You can also report an email before you send it to the trash. Flagging a suspicious email will help train the systems of email providers, which eventually would reduce the likelihood of phishing emails landing in the inbox of users.
You can report an email for phishing on most major services like Gmail and Outlook. For example, on Gmail, click on the three-dotted menu icon located on top of the email message, and click the "Report phishing" button. You can also directly forward a suspected phishing email to reportphishing@apwg.org, which is an address that belongs to the Anti-Phishing Working Group of the FTC.
If you have unfortunately fallen prey to a phishing attack and have entered your credentials on a fake website, immediately change your passwords. Preventing hackers from easily accessing your accounts is also why you should always enable two-factor authentication.