Windows Ping Of Death Exploit Returns, Patched In October 2020 Update
Bugs and vulnerabilities are pretty much part of software life and developers try their best to patch those up sooner or later. Sometimes, however, these problems pop back up, either in a new form or because fixes weren't applied to newer versions of the software. It's not clear which of the two was involved in this latest Windows 10 vulnerability but an old enemy has reared its ugly head again to drops users into Blue Screen of Death hell using relatively trivial methods.
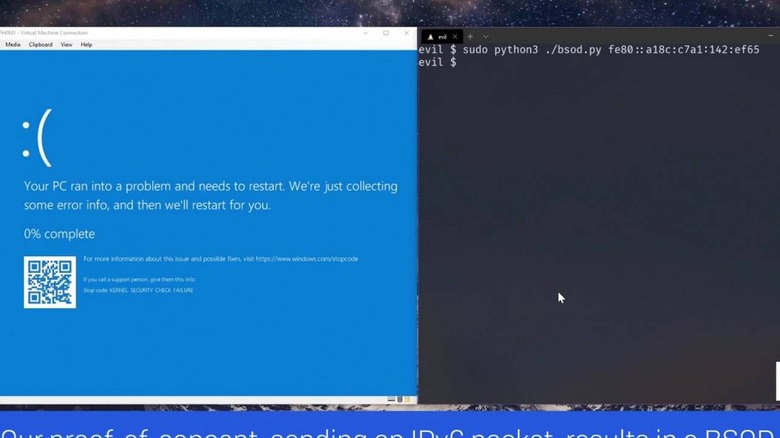
The Ping of Death vulnerability, as security company Sophos calls it, was actually fixed back in 2013. For reasons still unknown, it seems that Windows 10 in 2020 is just as susceptible to the exploit. And it doesn't take much to exploit it and bring someone's computer down.
At the heart of the Ping of Death is a flaw in Window's TCP/IP driver, the piece of software responsible for low-level network communication that underlies all communication the computer makes over both local and Internet lines. It involves a specially crafted IPv6 router advertisement packet that contains more data that the driver can handle, which, in turn, causes a buffer overload and a BSOD.
Fortunately, that vulnerability can be easily fixed by simply updating Windows 10 to the latest batch of security patches for October 2020. If that's not possible, there are also ways to mitigate it, like disabling IPv6 entirely, until it is possible to patch the computer. Windows warns that the vulnerability could also be used for remote code execution (RCE) but Sophos' tests showed it was not as easy as the denial of service (DoS) described earlier.
The security outfit also mentions another interesting bug fixed by the October 2020 patches, this time relating to Windows' own security catalog for verifying files. It is also comparatively easy for malware to spoof Windows' security system using this vulnerability, making it even more critical for users to update their PCs as soon as possible. Hopefully, these patches don't themselves introduce worse bugs.