Thousands Of Android Apps Bypass Permissions To Violate User Privacy
Unlike on regular desktop computers, the opportunities to gather information on users are greater on mobile phones. That's why platform makers have devices as a permission-based system to limit what apps can do and what they can access on the device. Android has gone a long way in refining its system to ensure that few to no abuses would happen. Unfortunately, it turns out that more than 1,000 apps have found a way around those restrictions, even after users explicitly denied them permissions.
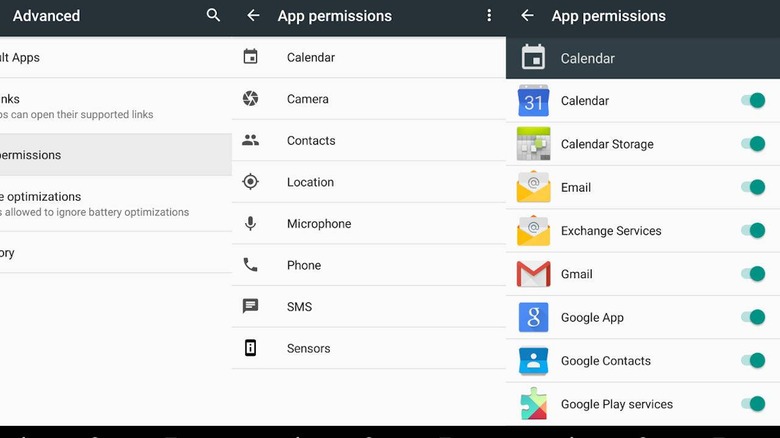
A flashlight app has no business accessing a phone's mic and while a third-party phone dialer will need to make calls, it may not need to track the phone's location, especially when not in use. Both iOS and Android implement a system where apps are granted or denied certain permissions. At times, it's even possible to revoke permissions that an app may actually need to function.
Unfortunately, it seems that not a few Android apps have found ways to ignore the user's explicit instructions in this regard. A research conducted by the International Computer Science Institute revealed that up to 1,325 apps on Google Play Store continued gathering data regardless of their permissions settings. Photo editing app Shutterfly, for example,, has been discovered to be getting GPS data and uploading it to company servers even without permission to access location data.
Rather than being a bug in Android's framework, these apps have used other means to workaround those restrictions. Some would use Wi-Fi connections and other data to infer certain pieces of information like location. 13 apps, in particular, were discovered to be piggybacking on other apps to read data stored on SD cards. Those 13 apps have been installed more than 17 million times.
The researchers notified both Google and the FTC of this matter last year and Google said it would be addressing the problems in Android Q. That, unfortunately, leaves users exposed until their OEMs roll out that update, presuming they even do so.