The Nintendo Switch Has Already Been Hacked Somewhat
That took long enough. When you have a super high-profile device that is also super closed, like the Nintendo Switch, you are practically giving hackers an open invitation to test just how strong your defenses are. Unfortunately, if you have a high-profile device, chances are, those defenses easily crumble under expert hacker hands. A little over a week since it launched, famed iOS jailbreaker qwertyoruiop has revealed he found a way inside the Switch, and hackers have to thank Apple for that.
What does Apple have to do with hacking the Nintendo Switch? It turns out that despite not having an actual web browsers available to users, the Switch still does have a web browser view necessary for performing captive portal logins. You know, those pesky logins required at some public or hotel hotspots? For that purpose, the Switch includes Apple's WebKit engine, the same open source engine powering Safari on Mac and iOS.
The problem is that the version that the Switch uses is an old one which was the same version that came with iOS 9.3. That particular version already has a known vulnerability that allowed the Pegasus malware to run rampant on iPhones. Apple patched that exploit in iOS 9.3.5 but, for whatever reason, Nintendo decided to go with an older one. Perhaps they just crossed their fingers no one would notice.
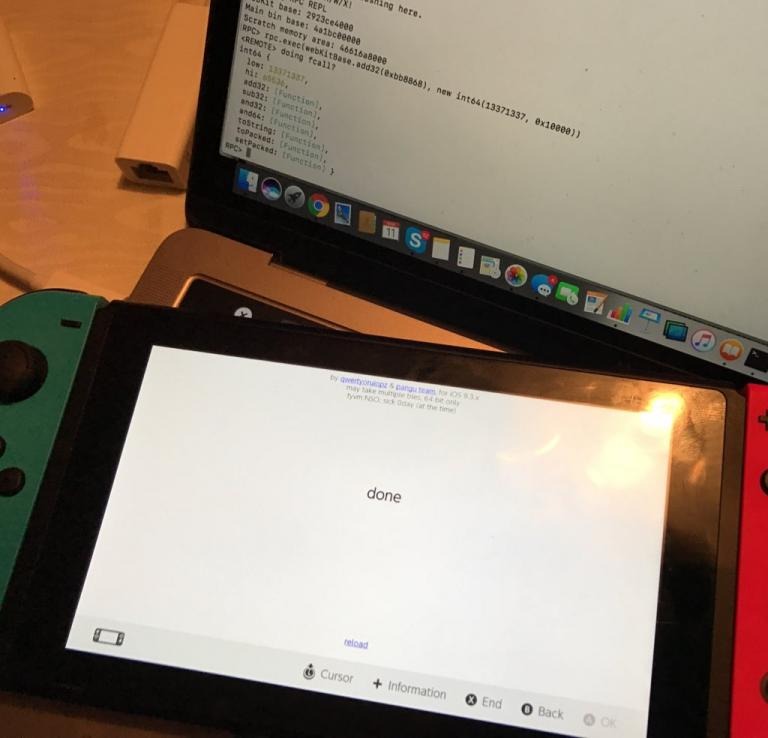
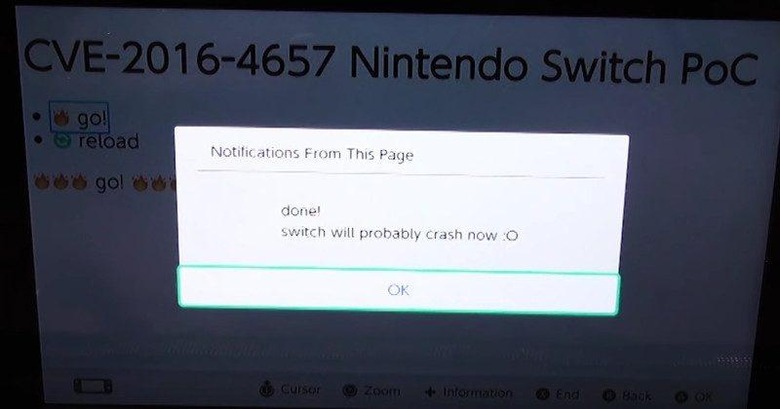
qwertyoruiop has had experience it the iOS 9.3 WebKit browser before to it wasn't too much work to modify his older exploit, strip it of iOS-specific code, and make it work for the Switch. He doesn't provide any proof of concept or a release, but LiveOverflow made a rather detailed video showin and explaining how the exploit works.
There isn't any need to celebrate yet, other than proving that Nintendo may have overlooked some possible holes in the Switch. The hack doesn't reveal much information yet or hand over control to hackers, but it's always a start. Unless, of course, Nintendo manages to quickly roll out an update patching WebKit.
VIA: Wololo.net