Tasker 5.9.2 Will Let You Run ADB Commands Without A PC
Android is an open platform but much of its functionality is still hidden behind superuser (root) access and sometimes esoteric commands. The latter, which can sometimes be used to enable or control features only available to rooted devices, often requires connecting the phone to a computer every time you need to issue the ADB command. The next release of Tasker will thankfully have a fix for that, making it even easier to perform advanced actions without having to root your phone.
To be clear, the Android Debug Bridge or ADB is primarily a development tool but, fortunately, Google hasn't shut the door on Android power users' faces (yet). The tool, which is run on the command line of a computer connected to a phone, is used to access certain settings or files that would normally be beyond the reach of users with unrooted phones.
Tasker won't be changing that requirement but Tasker 5.9.2, currently still in beta, will make it easier by allowing users to issue adb commands from within the phone without connecting it to a computer. There is, however, one important caveat. You do need to run one adb command on a computer for the first time as well as every time you reboot the phone. Technically, that command opens a port on the phone for listening to ADB commands and Tasker simply keeps it alive as long you don't restart the phone.
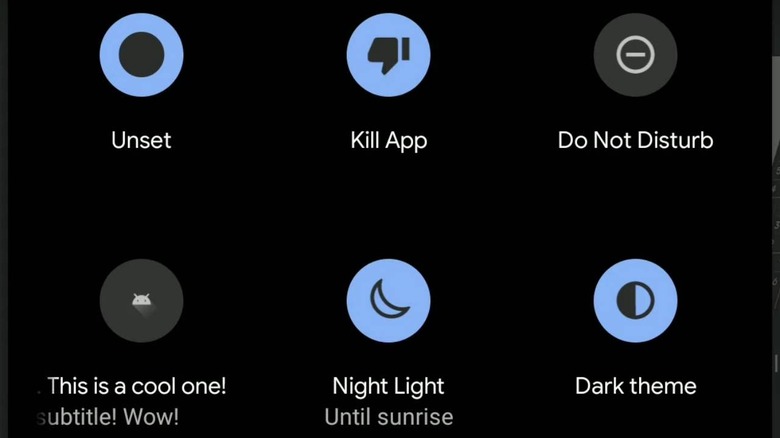
After that initial command, you can freely use adb as if the phone was still tethered to a computer. Of course, ADB alone doesn't give you full system access that is only possible with rooted phones but it does expose a few convenient functions without root. Those include managing app permissions, killing apps, or toggling mobile data and airplane mode, all of which can be tied to other Tasker actions.
Together with access to Logcat, which opened the doors for all sorts of event triggers, it seems that Tasker 5.9 is shaping up to be the automation platform's most important release so far. As with most of Tasker's amazing features, it isn't certain when such features will run afoul of Google, which may view them as abuses or potential security risks. Aside from a brief episode regarding SMS permissions, though, that hasn't happened in a grave way yet and will hopefully stay that way.