Installing Signal Isn't Enough To Make Your Chats Secure
Encrypted messaging apps may have gained traction over the past few years, but even if you use Signal your conversations may not be as secure as you think. As the indictment of former Senate Intel panel security director James A. Wolfe this week shows, overlooking a few key settings can make your messages all too easily accessed.
Wolfe was charged this week with lying to federal agents during an investigation into leaked classified information. Back in December 2017, he told the FBI that he had no knowledge of how three reporters were gaining access to non-public data. However, investigators later discovered that he'd used encrypted messaging app Signal, among other things, to share those secrets.
Signal launched in mid-2014, offering end-to-end encryption and identify verification to lock-down messages. Rather than requiring new user IDs, it uses cellphone numbers as account identifiers. One of the benefits of Signal's architecture, as revealed as a side-effect to a subpoena the service had received for a federal grand jury investigation in 2016, is that all it could reveal of a Signal user was the time their account was created and the last time they had connected.
There was some surprise, therefore, when the indictment documentation in Wolfe's case confirmed that details from his conversations with at least one reporter had been sourced from their Signal chats. "Between in or around September 2017 and continuing until at least in or around December 2017, Reporter #3 and Wolfe regularly communicated with each other using the anonymizing messaging application Signal, text messages, and telephone calls," the indictment reads.
Although unconfirmed, it appears that leaving one setting unchecked may have led to the unexpected Signal disclosure. Although chats on the service may be encrypted, they do not automatically delete. If investigators gain access to a phone, therefore – either yours or that of your contact – they'll see any messages sent and received that haven't been deleted.
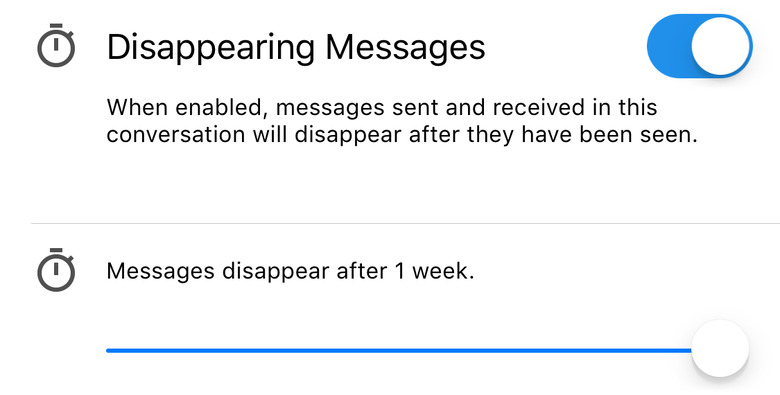
Signal offers an disappearing messages setting, added in late 2016. That automatically deletes the message off both devices, when it has been read, after a preset length of time. The company does point out that there's no way to stop the recipient from taking a photo of their screen before that happens, so it's not a perfect way to avoid documentation of your conversations, mind.
You'll also need to enable it on a per-chat basis: tap the contact's number at the top of the chat to access the settings, and turn it on from there. You can choose to have conversations delete after anything from five seconds through to a week. Signal also has the option to delete the whole cache, but you'll need to do that manually.
