Segway Hack: Hoverboard Fires Were Tip Of The Iceberg
Hoverboard fires weren't enough to deter some users from rolling these two-wheeled vehicles. Now we've got hackers taking to the streets, too. What one security company found in a popular Segway-brand Hoverboard will be enough to turn your stomach – or at least scrape up your knees as your Hoverboard is remotely commanded to stop, quite abruptly.
The device that's part of the study published this week by IOActive was the Ninebot by Segway miniPRO hoverboard. As the bans rolled in back in 2015 for other models not approved with baseline safety requirements, IOActive took a different approach. Instead of focusing on the hardware – which caught fire in some lesser-known brand models, IOActive looked to remote control with software and Bluetooth.
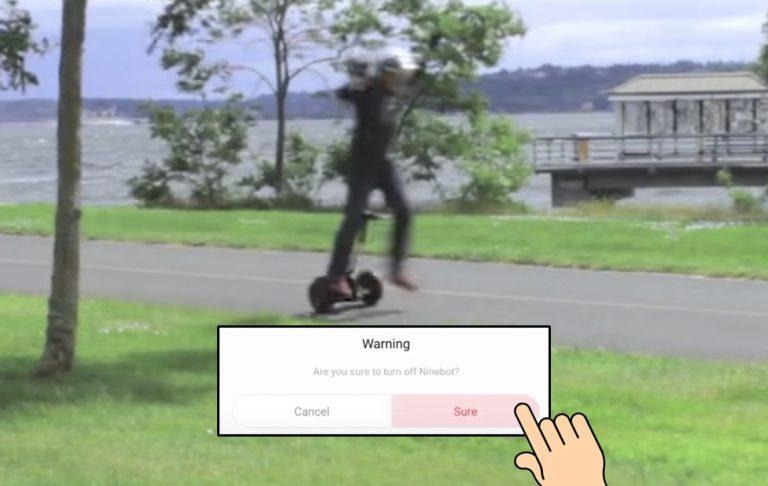
As IOActive researcher Thomas Kibride discovered, there's not a whole lot between a hacker and a hoverboard as a potential target. The results, as demonstrated in a handy video here – are entertaining to behold. Once the user gains access to the Hoverboard by bypassing the PIN code for Bluetooth pairing, the real fun begins.
"Regulations now require hoverboards to meet certain mechanical and electrical specifications with the goal of preventing battery fires and various mechanical failures," said Kibride. "However, there are currently no regulations aimed at ensuring firmware integrity and validation, even though firmware is also integral to the safety of the system."
While this set of vulnerabilities is tested only on one device, it's important to note that it is not just this device that users should be cautious with. The Ninebot by Segway miniPRO is currently one of the very few "Hoverboards" available and approved for mass sale in several large countries – including the USA.
Should you still avoid other hoverboards? Yes, absolutely – while they're regulated a bit tighter now than they were a couple years ago, there's still a BIG bit of potential for fire. Devices imported through online sources like Amazon and EBay are still quite vulnerable to less-than-reputable sources.
UPDATE: Before publishing the report in full through IOActive, the crew behind this study shared the vulnerabilities here with Ninebot. The company has since released a new version of the app in question and critical issues seem to have been remedied.