Security Issues In Some Android Handsets Leave Fingerprints Exposed
A team of researchers with FireEye have discovered a serious security vulnerability in some Android phones involving biometric security. The flaw leaves fingerprints open to hackers by storing them in a "world readable" folder as an image file. Both the HTC One Max and the Samsung Galaxy S5 were cited as vulnerable, but other Android phones from other manufacturers could also be at risk. The HTC One Max was cited as being the most vulnerable, however, storing the fingerprints as unencrypted BMP files that could be read by any unprivileged app or process.
[UPDATE] Word straight from HTC is as follows: HTC is aware of the FireEye report on fingerprint scanner security. We have already addressed the issue for the HTC One max in all regions, and it doesn't affect any other HTC devices. As always, HTC takes security issues very seriously and makes it a top priority.
The issues were recently detailed by FireEye Labs' researchers Yulong Zhang, Zhaofeng Chen, Hui Xue, and Tao Wei at Black Hat. A full 11-page report has been made available detailing the issue, all of which revolves around one big reality: "Once leaked, [fingerprints] are leaked for the rest of your life." Given that fingerprints are often associated with government-related documents, it is of particular importance that biometric security be top-notch.
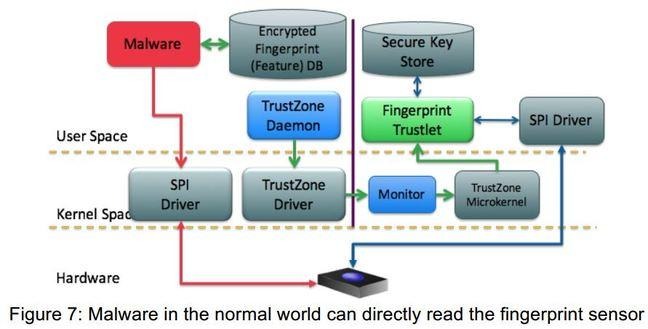
According to the report, the HTC One Max saves the user's fingerprint as "dbgraw.bmp" with world-readable permission. In addition, due to the auth framework refreshing the fingerprint bitmap with each swipe, hackers could "sit in the background and collect the fingerprint image" every time the user swipes. The researchers also found that "most vendors" do not properly lock down the fingerprint sensor, adding another level of vulnerability.
That latter issue, which would be mitigated by using the TrustZone protections offered by ARM chips, was also found to affect Samsung Galaxy S5 handsets, as well. At this time, both Samsung and HTC have pushed out patches to correct these vulnerabilities. Users are encouraged to keep their devices up to date at all times, while manufacturers are encouraged to utilize TrustZone protections and proper encryption.
