Researchers Outline Methods Of Stealing PC Encryption Keys Via Radio
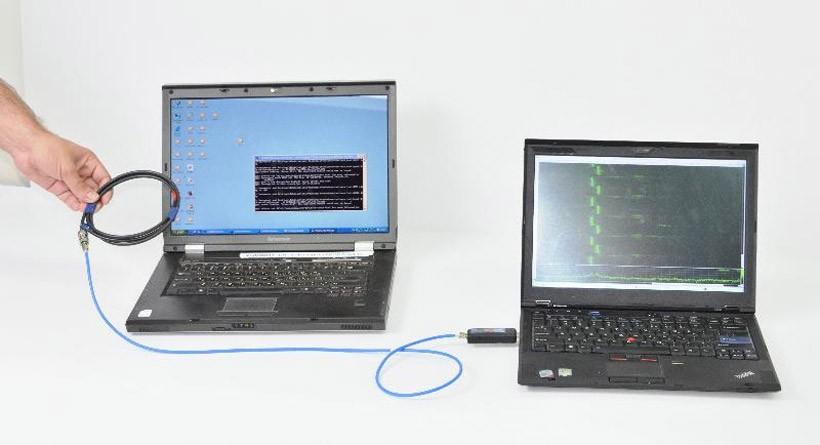
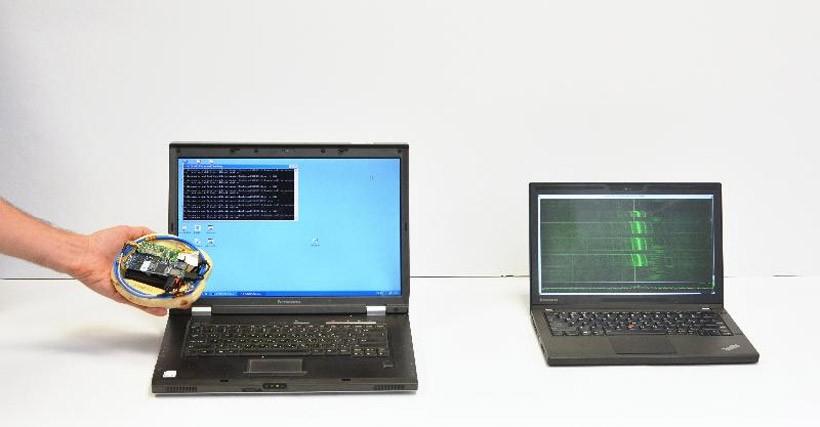
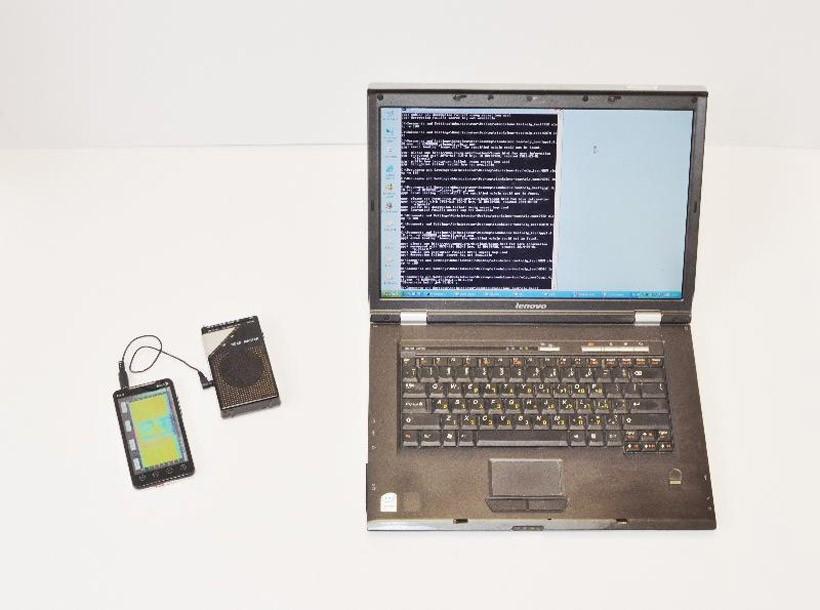
A group of researchers has outlined several ways that the secret encryption keys from a laptop can be stolen using a radio. For the theft to work the electromagnetic emanations from the notebook are measured non-intrusively using a radio from a distance of 50cm from the computer. According to the researchers, this attack can be carried out using cheap and easy to obtain equipment.
Among the items required to perpetrate this theft are a consumer-grade radio or a Software Defined Radio USB module. The setup can be operated in tethered or untethered mode and the hardware is small enough to be easily concealed inside pita bread or other small container.
Common laptops and popular implementations of RSA and EIGamal encryptions are vulnerable to the attack according to the team. Even modern version of these standards using exponentiation algorithms like sliding-window or side-channel resistant fixed-window are vulnerable. The team reports that they were able extract keys from laptops of various models while running GnuPG within a few seconds of commencing the attack.
The attack devised sends a few specific ciphertexts that are decrypted by the target computer and then trigger special values inside the decryption software. Those special values cause observable fluctuations in the EM field that surrounds the computer in a way that varies with the encryption key bits allowing the security key to be deduced. The images here show the three ways the researchers were able to steal encryption keys using their attack vector.
SOURCE: Tau.ac.il