OMG USB-C To Lightning Cable Is A Keylogger In Disguise
Most of the hacking incidents and security vulnerabilities we often see published happen remotely, often through malware that has been installed without the user's knowledge. Local Privilege Escalations or LPEs are often rarer because they need physical access to a target computer or device. There is, however, a very specific class of security attacks that involve a little bit of both, like in the case of an innocent-looking USB cable that will actually let a hacker see everything you type on a keyboard connected to it.
USB cables are a dime a dozen, especially ones that try to offer much cheaper alternatives to Apple's first-party accessories. One such example is a USB-C to Lightning cable that can be used to connect an Apple Magic Keyboard to a Mac or another computer. You might, however, be unwittingly buying a cable that will let hackers see anything you type through it.
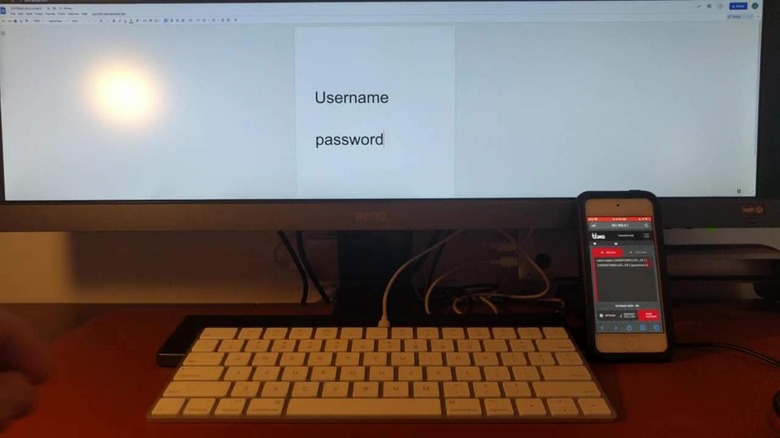
That's the rather frightening situation that the OMG Cable developed by security researcher MG tries to present. It does its work by creating a Wi-Fi hotspot that a hacker can connect to in order to record keystrokes going through the cable and probably other pieces of data as well. This isn't the first keylogging cable that MG developed, but it is the first to use USB-C.
The OMG Cable was developed partly as a response to claims that the USB-C connector's small size made it safe from having such implants, something the MG has now debunked. The new cable even adds new features, like geofencing to turn on the implant when entering a particular area. Geofencing also goes hand in hand with an older self-destruct mechanism that can now be triggered when the cable leaves a particular scope of engagement.
Worrying as it might seem, you're probably unlikely to encounter the OMG Cable from respected third-party brands. It is also a bit of good luck that the pandemic and global chip shortage has made it more difficult and more expensive to manufacture hacking cables like this, though it's still a good idea to stay away from cheap knockoffs.