New Android Malware Spreads Via Malicious WhatsApp Auto-Replies
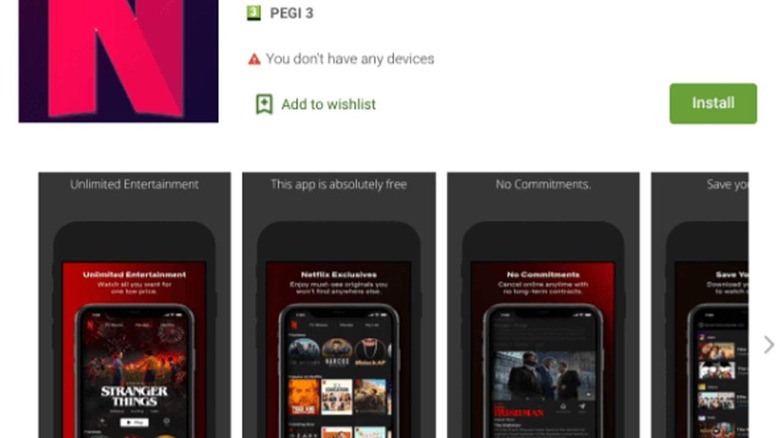
A new and malicious Android malware was discovered on the Google Play Store. The malware was disguised as a Netflix content enabling app called "FlixOnline." The malware spreads itself via malicious automatic replies to WhatsApp messages sent to the user. Payloads for the malware are received from a remote command and control server.Security researchers from Check Point say the new and innovative threat can send further malicious content via automated replies to incoming WhatsApp messages. Hackers could use the malware to distribute phishing attacks, spread additional malware, spread false information, or steal credentials and data from WhatsApp accounts and conversations. The app is masquerading as a service allowing users to view Netflix content from around the world on mobile devices.
Rather than doing what it promises to do, the malware monitors the user's WhatsApp notifications to send out automatic replies and receive content from its control servers. The malware message sent to victims via the auto-replies offers the users two months of free Netflix premium content at no cost anywhere in the world.
Check Point researchers say that when the application is downloaded and installed on Android devices, it starts a service that requests "Overlay," "Battery Optimization Ignore," and "Notification" permissions. After obtaining those permissions, the malicious app is able to create new windows on top of other applications, which are typically fake login screens for other apps to steal credentials.
Ignoring Battery Optimizations prevents the malware from being shut down by the battery optimization routine inside the device even when idle. Notification access allows the malware to access all notifications related to the device's messages and automatically dismiss and reply to messages on the device. With those permissions, the malware has all it needs to distribute malicious payloads and respond to incoming WhatsApp messages. Check Point notes that it did responsibly notify Google about the app and its research. Google did remove the application from the Play Store, but it was available for two months and was downloaded about 500 times.