Linux-Based Internet-Connected Devices Widely Vulnerable To New Worm
Symantec researcher Kaoru Hayashi has posted a report to the effect that a sizable portion of the "Internet of Things" is now vulnerable to a worm called Linux.Darlloz. The worm attacks CPUs running on devices like routers, set-top boxes, security cameras and industrial control systems, as well as PCs. The worm relies on a pre-May 2012 vulnerability still present in many devices running Linux.
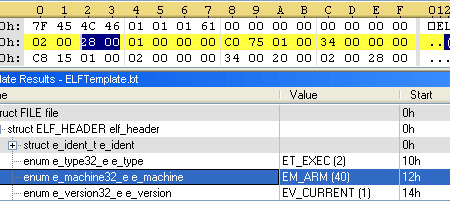
Up to this point, the worm only infects Intel x86 systems, but it has been modified slightly to cover variant architectures, including ARM, PPC, MIPS and MIPSEL. The above code shows that it affects ARM chips, as indicated by the "e_machine" value. This is just one of many examples found by Symantec.
The reason the worm could work so effectively is that many Internet of Things devices use chips that cannot be updated with the May 2012 patch that addresses the worm. The chips in question do not have the capacity to be updated. What's more, manufacturers of Internet-connected devices often do not disclose the existence of such update-limited chips on-board.
Hayashi offers this advice for all users of Internet-connected devices:
To protect from infection by the worm, Symantec recommends users take the following steps:
Verify all devices connected to the network
Update their software to the latest version
Update their security software when it is made available on their devices
Make device passwords stronger
Block incoming HTTP POST requests to the following paths at the gateway or on each device if not required:
/cgi-bin/php
/cgi-bin/php5
/cgi-bin/php-cgi
/cgi-bin/php.cgi
/cgi-bin/php4
SOURCE: All Things Digital