iPhone Tracking: Not New, But Already Used By Law Enforcement
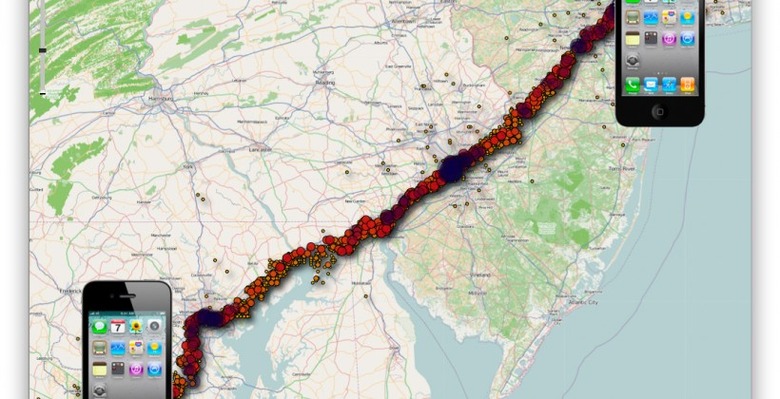
Fall-out from news earlier this week that the iPhone and 3G-enabled iPad maintain a comprehensive log of location data continues, with suggestions that not only are the revelations not as fresh as they're presented as, but arguments as to how dangerous the location collection actually is. Alex Levinson claims that the discovery of the "consolidated.db" database was in fact made several months ago, shortly after the release of the iPhone 4. The researcher also suggests that, contrary to much of the hype, the database itself is of relatively little importance, since Apple is not actually accessing it.
"Apple is not harvesting this data from your device" Levinson insists, stating that "through my research in this field and all traffic analysis I have performed, not once have I seen this data traverse a network." Instead, he claims the file has always been present, used as "a log generated by the various radios and sensors", but was simply moved when iOS 4.0 was released and then "rediscovered" by the other researchers.
The fact that the data is stored on the user's own machine and not accessed by Apple is one of Andy Ihnatko's key themes as well, suggesting that "the logfile's purpose is to track the performance of the phone and the network, and not the movements of the user." Nonetheless, he still describes it as "a nervous can of worms":
"This is an open, unlocked file in a known location in a standard database format that anybody can read. If someone has physical access to your Mac — or remote access to your user account — it's a simple matter of copying a file and opening it. And while the logfile can't tell someone that you were at a specific house, it can obviously tell your boss that you went to the Cape on the day you called in sick." Andy Ihnatko
Daring Fireball's John Gruber claims his insider-sources suggest that the database is a cache for location data and that historical data should, in fact, be being deleted as time goes on. That such a process isn't happening is said to be most likely an oversight, and he's predicting it's addressed in the next iOS update.
However, that will be too late for those iPhone users who have already seen the database potentially used against them. Levinson told GigaOm that the location data is already being used by law enforcement agencies, and that while he wouldn't name specifics, they include "multiple state and federal agencies both in the U.S. and internationally." The fact that the data is – by default, though an option is available in iTunes – unencrypted means that physical access to a user's machine is likely all that's necessary to gain access to the location information.
Apple is still yet to comment on the story.