Infected Android Apps Downloaded By Thousands: Where Are The Users?
Another day, another Android malware sighted on Google Play Store. Countless pieces and analyses have been written up regarding Google's mostly hands-off approach to screening apps and it's a bitter pill to swallow for Android fans and believers. But while there's no denying that too many such Potentially Harmful Apps or PHAs have slipped through the cracks, there is also one thing that seems to escape notice: the hundreds of thousands of users that should have all been compromised by these malware-laden Android apps.
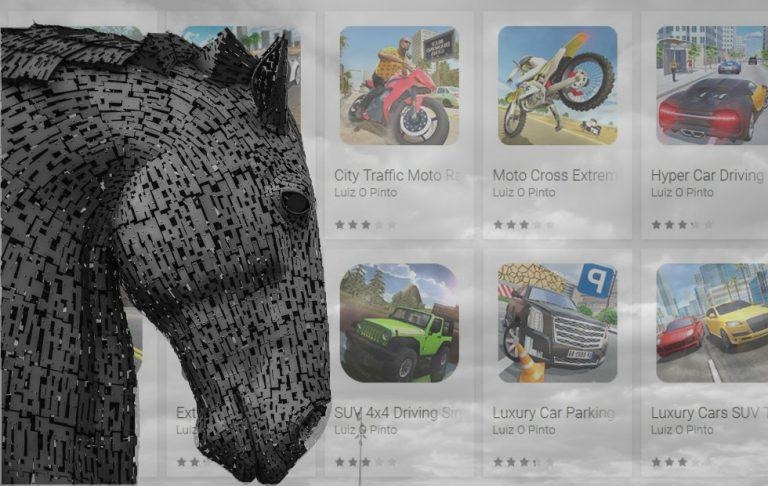
The latest report of apps bearing malicious gifts comes from ESET researcher Lukas Stefanko. According to his series of tweets, as much as 13 apps, all of them games and published by the same developer, have made it past Google's automated security checks. Two of these were even marked as trending. In total, these games have accumulated more than 560,000 installs between them. None of them actually work as advertised.
The apps seemed to crash when launched but, in fact, they connected to a remote server to download and install malware behind the scenes. The malware's exact purpose or modus is still unknown at this point. Regardless, the fact that the malware payload persists across reboots and can view the phone's network traffic is reason enough to be worried. Google has reportedly now removed the apps from the Play Store for violating its policies.
Don't install these apps from Google Play – it's malware.
Details:
-13 apps
-all together 560,000+ installs
-after launch, hide itself icon
-downloads additional APK and makes user install it (unavailable now)
-2 apps are #Trending
-no legitimate functionality
-reported pic.twitter.com/1WDqrCPWFo— Lukas Stefanko (@LukasStefanko) November 19, 2018
It's hard to argue with the figures as Google simply lists the number of times apps have been installed on devices. And this isn't even the first time PHAs have been spotted and reported on the Google Play Store. But with potentially millions of installs and potentially millions of infected Android devices, there is almost an eerie silence from users who have been conned into downloading these malicious apps. Where are they, then?
It's possible that these users are ashamed to come forward for having been so easily duped by the promise of free. Or they are living in ignorance of having been infected by such malware. One other plausible explanation, however, is that many of these users might not exist at all. If they did exist, you'd think they'd be making a big stink over how frequent these apps get into Google Play Store.
It's easy to point fingers but there are services and tools that can be purchased to game almost every system put in place to prevent fraud. Those can involve clicking or tapping on screens and ads or installing apps or even leaving fake reviews. Given how cheap the most basic Android phones are, it's not hard to imagine some shop somewhere providing such services, knowing full well the implications of such actions.

Photo courtesy of SCMP.
In other words, those hundreds of thousands of installs could very well simply be inflated numbers with very few actual affected users. Considering two of the apps in this most recent case are trending without even being a notable game is enough to suspect the real damage the PHAs are doing. In fact, it makes it even more dangerous because security researchers aren't able to determine the actual impact apps and malware have on actually existing users.
This doesn't let Google off the hook, of course. In fact, it only makes its lapse even worse. Not only were PHAs carrying malware able to get into the Play Store, they were also able to artificially boost their installs to make them look popular. While this particular case may not have done as much damage as actual exploits in the wild, it proves how Google's systems are easily gamed despite the policies it has in place. They might be small incidents, but they slowly chip away at whatever confidence or trust Android users have left over Google Play Store's mechanisms.