Google Chrome Hacked At $1m Pwnium Contest
Eric Schmidt may have claimed that Google's Chrome browser is "by far the safest" at his MWC 2012 keynote speech last week, but that hasn't stopped an enterprising student from finding an exploit at CanSecWest Pwnium, an alternative to the Pwn2Own contest.
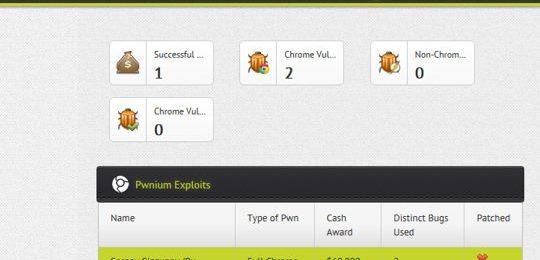
The Russian university student, Sergey Glazunov, managed to bypass Chrome's sandbox and exploit two vulnerabilities in the extension sub-system. Glazunov finds bugs in the browser as part of Google's bug bounty program, and was commended for his research work, as well as the exploit itself.
Talking to ZDNet, Justin Schuh, part of Google's security team, said:
It didn't break out of the sandbox [but] it avoided the sandbox. It was an impressive exploit. It required a deep understanding of how Chrome works. This is not a trivial thing to do.
Glazunov's reward for finding the exploit? A cool $60,000. Google also noted that the exploit would be fixed via an update to the browser which will be pushed out automatically.
Pwnium is an alternative to the traditional Pwn2Own contest, set up specifically to find exploits in Google's Chrome browser, as opposed to Pwn2Own which includes Internet Explorer and Firefox. This is the first time in four years that Google's browser has been hacked, with competitors browsers being successfully hacked in the past.