GO SMS Pro On Android Has Been Leaking Users' Shared Files For Months
Google made a big splash about the completion of the global rollout of RCS and its next steps to ensure its security on Android via end-to-end encryption. Coincidentally, this latest bit of security news highlights why this development is critical in a post-SMS world. A once-popular alternative SMS app on Android has apparently been exposing any photo, video, or file that its users have been sharing and its developers have conveniently gone silent when notified of the security lapse.
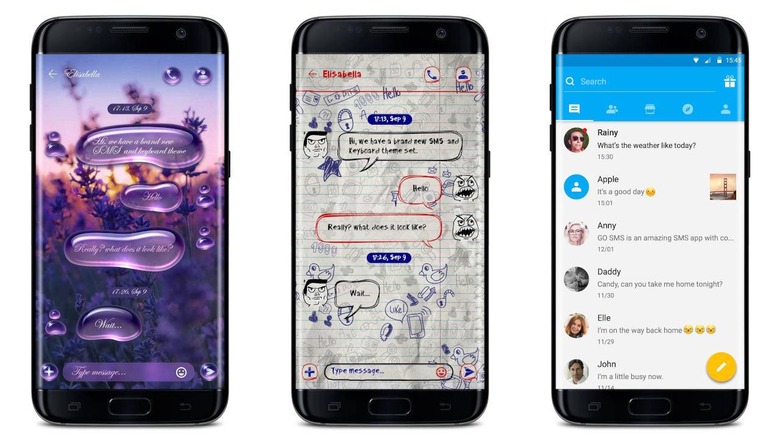
GO SMS Pro, which is just one of many GO-branded apps available on Google Play Store, reach the height of popularity in the earlier days of Android when third-party SMS apps were all the rage. These apps tried to offer advanced features beyond what plain old SMS could support, like sharing photos and videos with other users. The way the app implemented this was quite trivial but, unfortunately, also insecure.
The app apparently uploaded the shared files to a remote server and generated a URL so that anyone can view the file even if they aren't using GO SMS Pro. Unfortunately, that "anyone" turned out to be literally anyone since the files were unencrypted and the links to them were simply numbered sequentially in a predictable manner. In other words, once someone with skill got hold of one such link, they could easily just go through all the files stored on the server, which included screenshots of confidential and private information.
Making matters worse is that the developers of the app have been completely unresponsive to the report. Trustwave, who discovered the issue, reached out to the developers in August as part of due disclosure procedures. One email bounced back and no response was received. After three months, the security researchers decided it was time to go public with the vulnerability.
Admittedly, this behavior isn't something that Google Play Store's security checks would have easily caught as it is a server-side behavior. It might not even be against any Android policy, though it makes the rather blatant and gross error of not employing security best practices in the first place.