Fortinet VPN Hacker Leaks 500,000 Users' Passwords
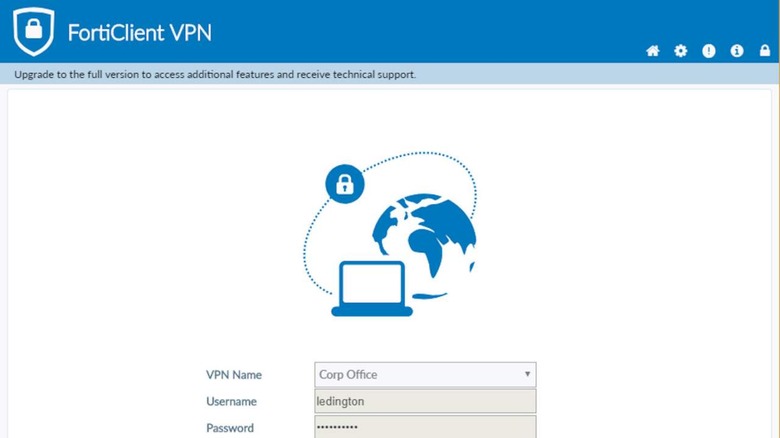
Virtual Private Networks or VPNs have long been used to hide one's actual location and activities on the Internet, either for security purposes or for bypassing region locks. It is one of the standard arsenals in network security, but a VPN isn't a bulletproof solution, especially if the VPN itself is the one that gets hacked. That's the nightmare scenario that users of the popular Fortinet VPN product are now finding themselves in after a hacker just dumped 500,000 user names and passwords on the Internet for absolutely free.
VPNs naturally run on remote servers and, like any computer service, can be targeted by malicious agents. Last April, servers running Fortinet's FortiOS were reported to be under attack by state-sponsored actors. It seems that the same vulnerability was exploited by at least one hacker who has now simply leaked the payload for any other hacker to use.
That threat actor has been identified as "Orange," the leader of a new RAMP hacking forum and a new Groove ransomware operation. Orange reportedly broke off with an older Babuk ransomware gang to establish RAMP and Groove. Perhaps to promote the new operation and recruit other hackers, Orange simply leaked almost 500,000 passwords to show off.
Those 500,000 credentials include logins and usernames of Fortinet VPN scraped from vulnerable devices in the past months. While the exploited vulnerability has already been patched by now, the credentials are actually still in active use. BleepingComputer confirmed that the IP addresses are linked to Fortinet VPN servers, while a source verified that some of the leaked passwords are still valid.
This leak, of course, puts the security and integrity of Fortinet VPN servers at risk considering these can be used by hackers to further steal data or install ransomware on other computers. Unfortunately, the only recourse at this point that can be taken is for server owners to force reset all users' passwords in order to close the holes that the leak has laid open.