First Full OS X Ransomware Seen In Transmission BitTorrent App
When speaking of malware, Windows is usually the poster boy for an OS that gets infected a lot almost by nature. In truth, however, no operating system is totally bulletproof. Even Apple's OS X and iOS, usually considered to be tightly guarded silos, have their fair share of intrusions. This latest incident is one such example but this time the affected platform is Apple's much larger Mac OS X. Named by security firm Palo Alto Networks as KeRanger, the ransomware's damage is worsened by the fact that it infected even legitimate installers of the Transmission BitTorrent client.
The KeRanger ransomware is special in two ways. First is that, unlike most malware that you get from downloading and installing shady software or software from unofficial sources, KeRanger actually infected the DMG files available from Transmission's own server. The second way it is significant is that Palo Alto Networks considers this the first fully functional ransomware that has infected OS X computers. Others before it, like FileCoder, were considered incomplete.
Like any other ransomware, KeRanger's goal is to secretly encrypt users' files and then demand a hefty sum in exchange for decrypting them. In order not to throw of users immediately, KeRanger actually waits for three days after the infected Transmission app has been installed before it contacts its command and control server and does its dirty work. KeRanger is no simple ransomware, however, as it seems to still be in active development. It also tries to target Time Machine backups so that users won't even have the option to restore a clean backup.
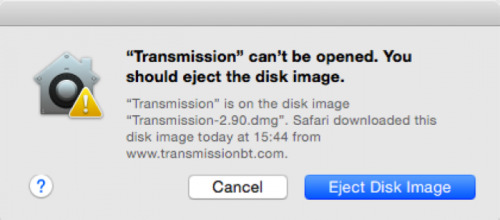
KeRanger is able to evade Apple's Gatekeeper security utility because the installer has been signed with a legit Mac app certificate. Fortunately, Apple has immediately revoked the certificate and updated XProtect with the new malware signature. Transmission has also removed the infected installer but those who downloaded the new Transmission 2.90 between March 4, 11 a.m. PST and March 5, 7 p.m. PST might have been infected.
The worry part about this whole incident is how KeRanger was able to silently infect even legitimate installers coming from the main source and makers of the software, whereas most malware get acquired by downloading software from unofficial sources. It is definitely a wake up call for developers and software distributors to ensure that the software they are distributing is clean.
SOURCE: Palo Alto Networks