Faxploit Turns Archaic Technology Into A Security Risk
The combined might of email, scanners, and computers should have made the venerable fax machine obsolete right? Millennials might laugh at it and presume it went the way of the floppy disk but it might shock them to know that more 300 million fax numbers still exist. That may not mean that all of those are in use but it at suggests that some may be active and may even be connected to some network, be it local or the Internet. And that is one gaping security hole waiting for some enterprising hacker to get through.
To be fair, the fax protocol was made in the 90s and couldn't have predicted how the Internet would explode. Although the protocol was updated to add features, the protocol just wasn't made for the Internet age and especially an age where anything and everything is connected to some network.
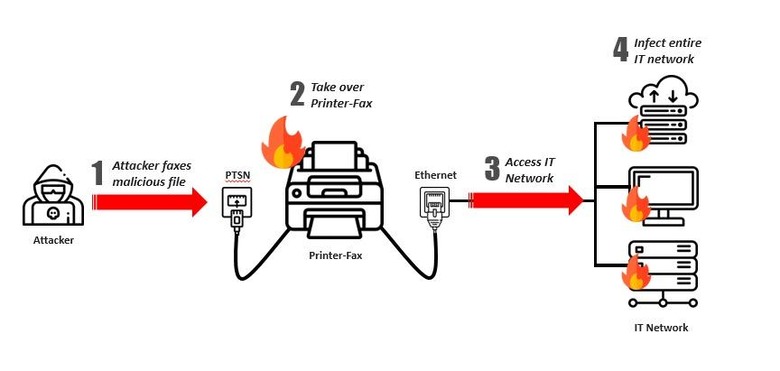
It's further complicated by the fact that most modern fax machines just aren't fax machines. In most cases, they are part of all-in-one printers that, by nature, are often connected both to the Internet and to an office local network, for example. They also often run very small real-time operating systems, which are ripe for the hacking.
That's the worrying discovery that Check Point Research made when testing the theory. Although they mostly tested it on HP all-in-one printers, they believe that any connected fax machine is vulnerable to this exploit. All they need is to be connected to a phone line on one end and a local network on another. Simply sending a malicious fax would allow a hacker to infiltrate and infect that network.
Responsible security researchers as they are, Check Point worked with HP to get the vulnerabilities in its all-in-one printers patched up before going public with the exploit. Owners of such HP printers just need to make sure their printers' firmware is up-to-date. No other printer brands were named, leaving one to guess whether those are just as vulnerable and, more importantly, now secured.