Facebook API Bug Exposed Photos Of Millions Of Users
Facebook's seemingly never-ending string of privacy and security scandals continues today. The company has announced a security flaw in its photo API that has affected as many as 6.8 million users. This bug potentially exposed user photos to apps that use the photo API, even in some cases impacting photos that were never posted.
According to Facebook, the bug gave third-party apps using the photo API access to a broader set of photos than they would regularly be able to see. While photo API apps usually only have the ability to access to Timeline photos, this bug also gave them access to Marketplace and Story photos. In some cases, the bug even exposed photos that were uploaded to Facebook but never actually shared anywhere.
Facebook says that the bug was present in the photo API between September 13 and September 25, 2018. "Currently, we believe this may have affected up to 6.8 million users and up to 1,500 apps built by 876 developers," Facebook said today. "The only apps affected by this bug were ones that Facebook approved to access the photos API and that individuals had authorized to access their photos."
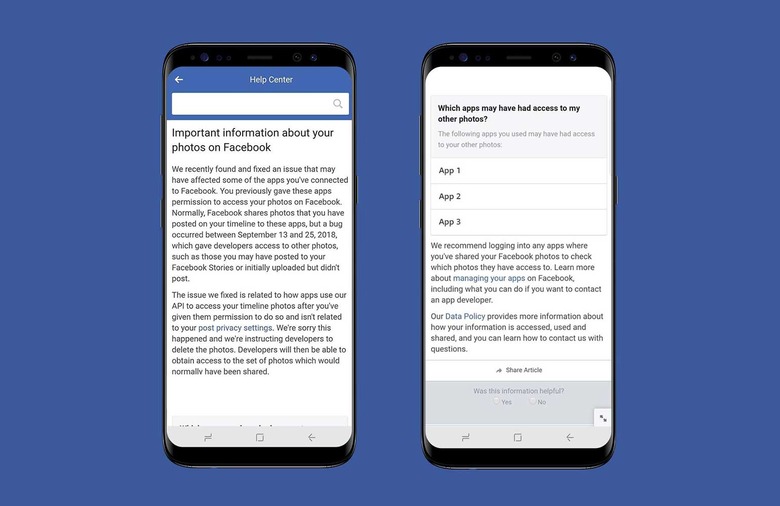
The company apologized for the bug with a simple "We're sorry this happened," and noted that it will soon begin working with these third-party app developers to figure out which users were affected by this bug. It will also notify people who were potentially affected through a Facebook alert, which you can see above.
So, if you see that alert pop up at some point in the next week or two, you'll want to log into the apps it lists to see which photos they have access to. At this point, one has to wonder when Facebook is going to stop unintentionally exposing user data, as the company's 2018 just seems to one controversy after another. Hopefully this is the last we hear about Facebook breaches and bugs for a while, but we won't exactly be surprised if it isn't.
