ExpensiveWall Android Malware Sneaks Into Google Play Store
It seems almost too ironic that the Google Play Store has been secretly invaded by even more malware after it has promoted its Google Play Protect security platform for Android. Boasting of technologies like machine learning and artificial intelligence, Play Protect promises to protect Android users more thoroughly without having to increase manpower. Alas, it seems that another malware, named ExpensiveWall, has gotten past the Play Store's security and this lapse is costing users a lot more than just peace of mind but actual money as well.
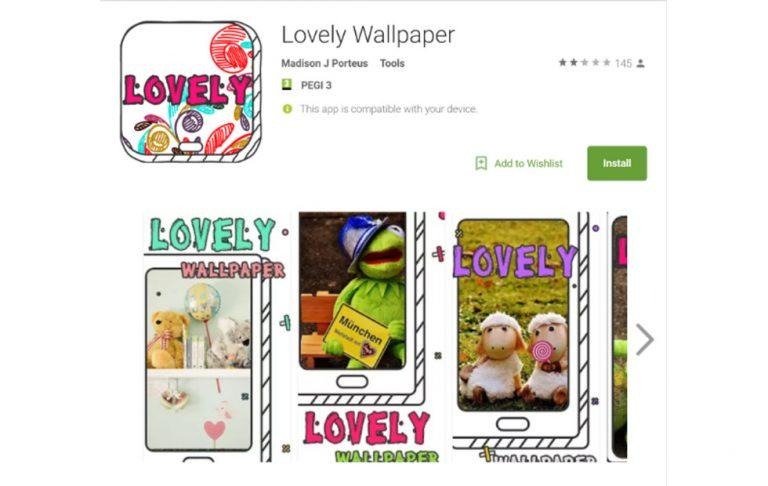
Check Point, the cybersecurity firm who reported this latest news, says that ExpensiveWall, named after one of its carriers, "Lovely Wallpaper" is actually a new variant of another malware discovered earlier this year. Both types of malware care costing users money by silently signing them up for premium subscriptions or sending premium SMS. Both strains have also made it past Google's security checks and have been downloaded thousands of times by users.
In fact, ExpensiveWall itself made it to Google Play Store twice. Check Point alerted Google to the presence of some infected apps on Google Play Store early August, at which point Google promptly took those apps down. However, days later a fresh batch of such apps reappeared and was again removed, but not before infecting at least 5,000 devices.

ExpensiveWall and its predecessor apparently made use of the same "gtk" toolkit, not to be confused with the open source GTK+ framework. Where ExpensiveWall differs is that it uses a "packed" version, that is, an obfuscated and encrypted version of malicious code, which helps it bypass Google's automated malware checks. Once the app has been installed from Play Store, it asks users for access to the Internet and to send SMS, permissions common to many Android apps and often taken for granted. The rest is history, as they say. And while this particular strain seems to be only designed for immediate profit, it might not take long for it to be turned into a more potent hacking exploit.
Although Google has taken down infected apps, at least those that it knows of, the apps naturally remain on unsuspecting users' devices. Google needs to step up its security game and find convincing ways to assure Android users that its Play Protect frameworks is better, or at least just as good, as laborious manual screening.
SOURCE: Check Point