Android Spyware Masquerades As A System Update
Malware of all kinds on Android are nothing new. Some even manage to get past Google Play Store's security checks. Most, however, ride on apps that are sourced outside of Android's sanction app store and those are often able to wreak more havoc than normal harmful apps. Case in point is a new kind of spyware that could be one of the more sophisticated malware of its kind in recent months, not only gaining access to almost all of a user's data but even conning them into thinking it's a legit system update.
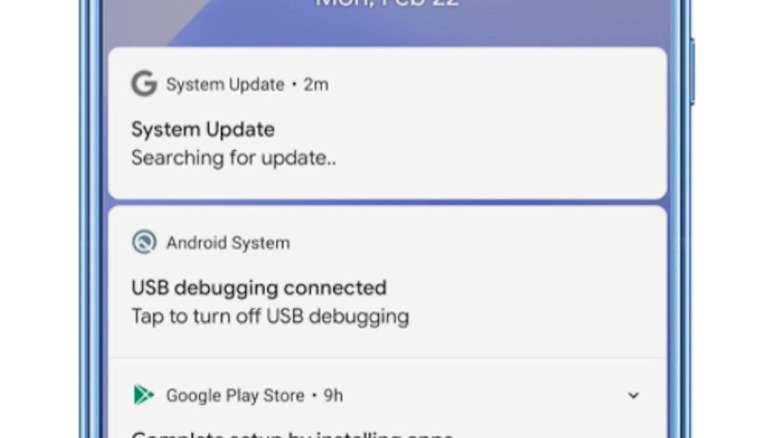
Many malware try to deceive users through various means, from pretending to be a free copy of a game or app, making users tap on areas of the screen to give the app system permissions, and more. This still-unnamed spyware, on the other hand, boldly shows up on the user's notification panel while it's running but makes them believe it's a legit system process. While that deception is almost amusing in its simplicity, its effectiveness and capabilities are no laughing matter.
According to security researchers from Zimperium, the Remote Access Trojan or RAT operates in a sophisticated manner rare among its kind. It can have access to a wide range of user data once installed, including messages, clipboard content which may sometimes contain passwords, images and videos, and more. It can even record audio and calls.
The malware has various mechanisms that allow it to bypass normal security measures. It scrapes screen content from encrypted messaging services like WhatsApp, for example, and only sends thumbnails rather than the full-sized images to avoid suspicious network behavior. The sophistication of the malware leads the researchers to suspect that it is part of a targeted attack rather than a generic widespread campaign.
The one good news is that this spyware wasn't found from any app in Google Play Store, serving as yet another cautionary tale about installing Android apps from unofficial sources. Then again, some malware do make it to Google's app marketplace but it will now be on guard against this particular RAT.