AirDrop Leaks Users Numbers And Emails Says Researchers
Apple has a few enviable features that other platforms, especially Android, still try to implement. The simple convenience and presumed security of AirDrop is one of those and it wasn't until last year that Android's Nearby Share finally caught up. Unfortunately, it seems that AirDrop isn't really that secure after all and the simple act of opening the share sheet in macOS or iOS is enough to have the user's phone number and email address leak to any hacker within range.
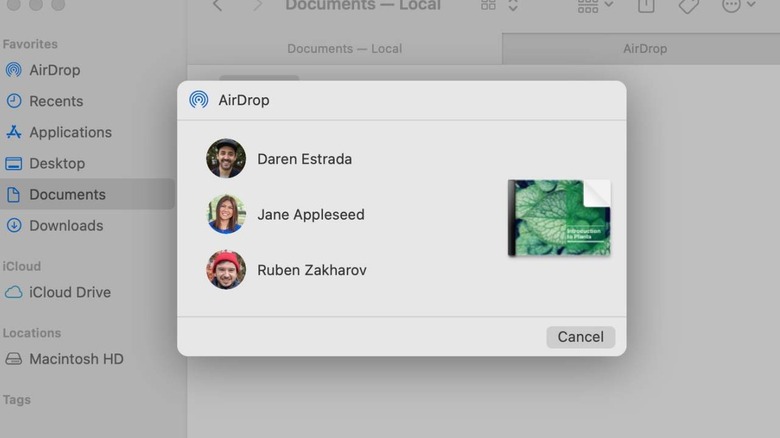
Although now more common, AirDrop uses a once novel technique that employs both ad-hoc Wi-Fi and Bluetooth to scan for devices and establish a connection between them. Users have the option to share only with their contacts or with anyone with a Mac or iPhone or no one at all. Unfortunately, the flaw found by security researchers doesn't even require actually using AirDrop to trigger the leak of personal information.
All that users need to do is to start the sharing process which brings up the macOS or iOS share sheet. Behind the scenes, AirDrop actually starts scanning for devices by broadcasting an encrypted packet of data containing the sender's phone and email address. The intention is to check which devices in the vicinity have the sender's contact also saved to qualify as a recipient.
Unfortunately, that encryption apparently isn't that strong and it is almost too trivial for hackers to perform a brute-force attack to decrypt numbers and email addresses. More worryingly such hackers only need to sit around, waiting for anyone with a Mac, iPhone, or iPad to start sharing anything to intercept the data. These phone numbers and email addresses can then be used for other attacks like phishing scams.
The researchers reportedly disclosed this vulnerability to Apple in 2019 and even provided an open source reference implementation of a more secure alternative. Apple hasn't replied to date and it's probably not that trivial to fix such an integral part of its macOS and iOS experience.