Internet Explorer Continues To Threaten PC Users With 0-Day Exploit
Microsoft has already thrown in the web browser towel and has based its Edge browser on Chromium and it seems to be in a rush to put its past behind it. Perhaps even too hastily. It may now be practically dead with less than 10% of the browser market, but a recently revealed exploit continues to put users at risk because of IE's unique position. And Microsoft claims to be not in a rush to patch that up.
The exploit revolves around a file format that very few probably remember by now. They're called MHTs and they're the special format that Microsoft once used when saving web pages in Internet Explorer. These days, web pages are saved as proper and standard HTML files but browsers, like IE, still retain the ability to open them.
MHT files have two special properties. One is that they automatically open in Internet Explorer. The other, according to security researcher John Page, is that a specially crafted MHT file can grant remote agents (hackers) access to local files just by opening the file. It can even be made to turn off any warnings about ActiveX Objects (another prehistoric technology) or requiring user interaction.
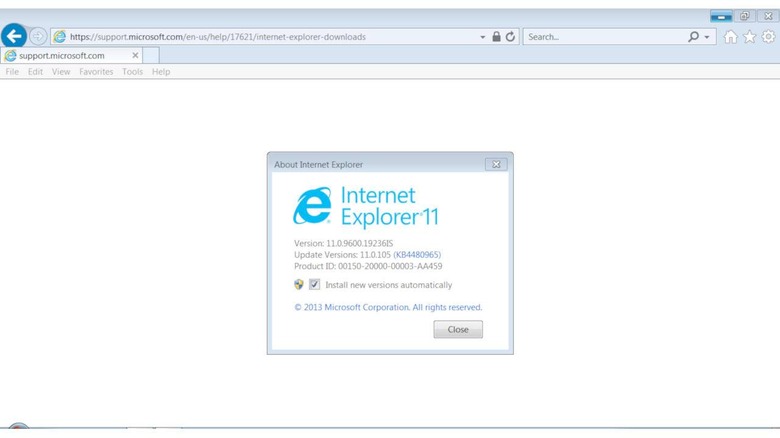
The vulnerability affects Internet Explorer 11 on Windows 7, Windows 10 and Windows Server 2012 R2 and Page reported the exploit late last month. Microsoft, however, responded by saying it won't be fixing the bug immediately and will consider it in the future. You might think that it's not that big of a deal considering how few users IE has left, but that's not exactly relevant in this case.
For one, there are indeed businesses that still use it for its compatibility with technologies that Microsoft has locked them into using for decades now. For another, Internet Explorer is still installed, sometimes even pre-installed, on all Windows systems. All it takes is for a user to double-click on an MHT file for whatever purpose and the rest is in the hands of hackers.