This Infamous Hacking Device Just Got An Upgrade
One of the most powerful USB-based keystroke injection devices, the USB Rubbery Ducky, has received a major upgrade that makes it even more menacing. Touted as the device that pioneered the technique of keystroke injection years ago, the latest iteration of USB Rubber Ducky introduces the improved DuckyScript 3.0 programming language with a host of dangerous new tricks in tow.
So far, the attack vector had to be attuned to the specific OS and version, but thanks to DuckyScript 3.0, the USB device can now recognize the OS details on its own and accordingly deliver the payload script. That is made possible with the latest suite of upgrades to the DuckyScript programming language, which now offers the flexibility of writing "if this, then that" type of commands. Based on the device environment, the USB Rubber Ducky will identify the system properties and deliver the right script to do its job.
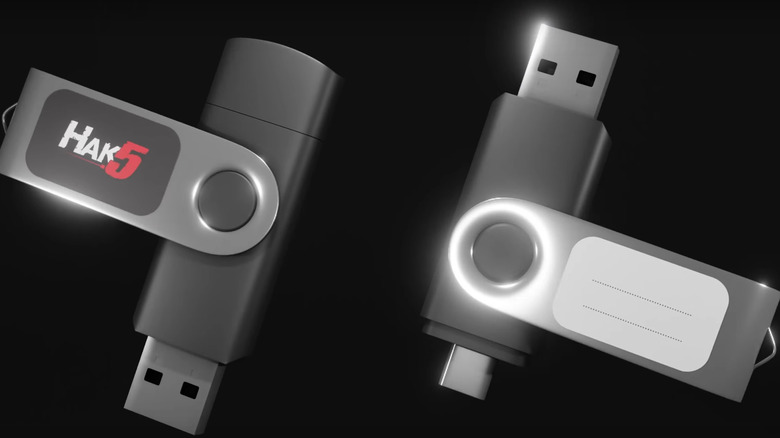
The latest version of the Rubber Ducky flash drive — which costs $59.99 each — relies on a technique called Keystroke Reflection to copy sensitive data like login credentials. Developed by Hak5, this new technique does not depend on system vulnerabilities to do its job. Instead, it exploits the very system design — that is, the directional keyboard architecture that dates back to 1984. All of that happens without alerting the target computer as the flash drive remains virtually invisible to the system.
A complete package in a tiny flash drive
At the heart of USB Rubber Ducky's destructive potential is its ability to pass itself off as a Human Interface Device in the same way a keyboard is recognized by a computer. That means every script injected by the USB device is treated by the system as a command from the keyboard. Then there is the payload studio, which is essentially an integrated development system for all Hak5 gear where you can write custom scripts and variables for a wide range of attacks. There is, for example, a script payload that can be delivered by the USB Rubber Ducky to a target computer in order to extract Chrome browser credentials without raising any alerts.
Hak5 has also posted a slick launch video on YouTube that details some of the product's key features. Creator Darren Kitchen calls it a passion project that has been in development for the past couple of years. To go with the hot new hardware, the company is also selling a new textbook that is a lot more detailed alongside the new Payload Studio software package that details how to create custom scripts, and an online course taught by Kitchen himself. As capable as it sounds, you're probably not at the risk of being attacked with a USB Rubber Ducky unless a bad actor gains physical access to your computer. So, as long as you don't plug in any random USB stick in your computing machine, you're likely safe.