2017 Petya Malware Actually Irreversibly Wipes Data
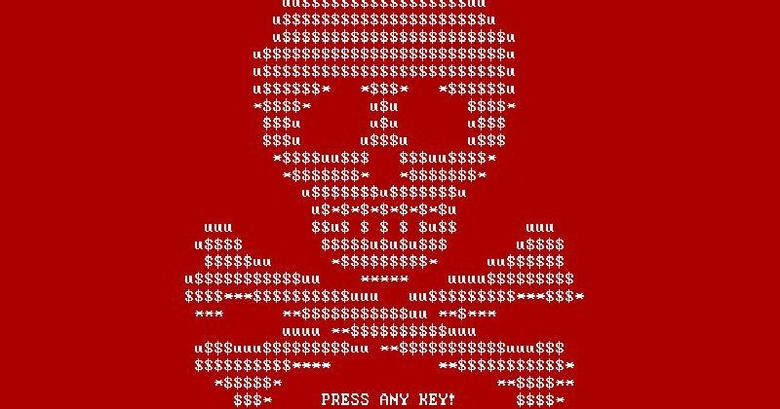
It smelled like a ransomware and talked like a ransomware but, in fact, it was worse than a ransomware. Although it has been labeled as a strain of a 2016 ransomware, this year's "Petya" malware has been mislabeled. According to cybersecurity outfit Comae Technologies, the so-called Petya.2017 is actually a wiper masquerading as a ransomware, doing irrecoverable damage to data on drives. To add insult to injury, this wiper was specifically designed to look like the first Petya in order to fool media into thinking that it is.
The original Petya was already different from most ransomware in that, instead of simply targeting individual files, it made entire drives inaccessible by modifying the MBR or master boot record of the drive. Think of the MBR as the table of contents of a hard drive that describes the layout and content of the data storage. What the 2016 Petya did was to basically read the first sectors of the drive and encrypts them, which allows the MBR to be restored to its original state after the ransom has been paid.
This Petya.2017, in contrast, doesn't encrypt the MBR or saves its data for later retrieval. It simply trashes the first 25 sectors blocks of a disk. And unlike a book that can still be read even without a table of contents, a data drive can't when its MBR has been scrambled. In other words, there is no way to retrieve the data on the drive at all.
This dashes whatever hope infected users had left to recover their data, as if things weren't bad enough. Some have already paid the ransom only to be foiled by the fact that the e-mail that should have been used to contact the hackers have been shutdown by the email provider. Not that it mattered after all, since there was no way to recover their files anyway.
The malice behind this version of Petya lead Comae Technologies to believe that this wasn't a for-profit operation. Instead, it may have been specifically designed to steer the media narrative away from seeing it for what it truly is: a veiled nation state attack against Ukraine, where the malware originated and where it has done the most damage.
SOURCE: Comae Technologies