10 Million Android Users Infected By Barcode Scanner Adware Via App Update
Security company Malwarebytes has reported that late last December, it began getting distress calls from forum patrons. The company says that these forum users were experiencing ads opening via their default browser out of nowhere. The strangest part about the ad serving outbreak was that none of them had recently installed any apps, and all apps that were installed came directly from Google Play.
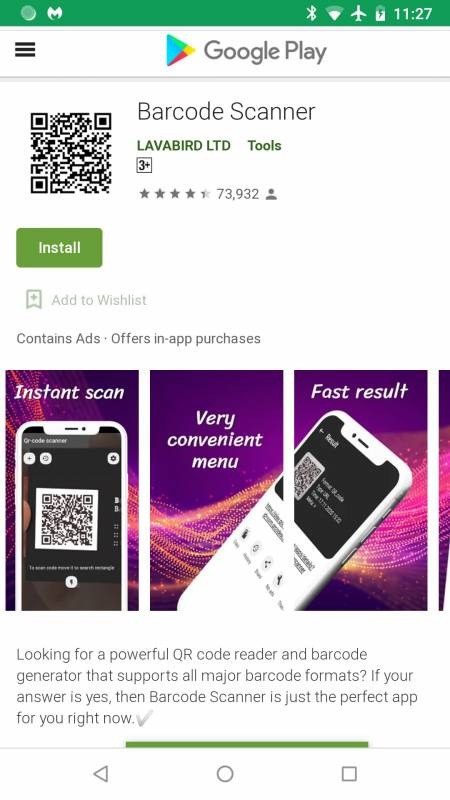
Google has a notorious history of being unable to ferret out all malicious apps on Google Play, so using only the official Google Play store certainly doesn't rule out being infected with malicious apps. Malwarebytes says that one of its form users called Anon00 discovered that the ads are coming from an app installed for a long time called Barcode Scanner.
The app had been installed over 10 million times from Google Play. Malwarebytes said that it quickly added the detection, and Google remove the app from the store. Many users that the app on their mobile devices for a long time, including one that had the app installed for years. After an update issued in December, Barcode Scanner went from exactly what it claimed to be to complete malware.
The update was believed to have been issued on December 4, 2020. Malwarebytes says that most free apps on Google Play include some sort of in-app advertising using an ad SDK. The security company says every now and then, an ad SDK can change something on there and add start getting aggressive. Malwarebytes is clear that when that happens, it's not the app developers who are the culprits, but the SDK company, but that wasn't the case for Barcode Scanner.
In this instance, malicious code has been added that wasn't in the previous version of the app, and it used heavy obfuscation to avoid detection. It was verified to have been offered by the same developer as it uses the same digital certificate seen in previous clean versions. Barcode Scanner has been removed from Google Play but could still be on millions of Android devices.
