Trustwave Finds Most Common Business-Compliant Password Is Password1
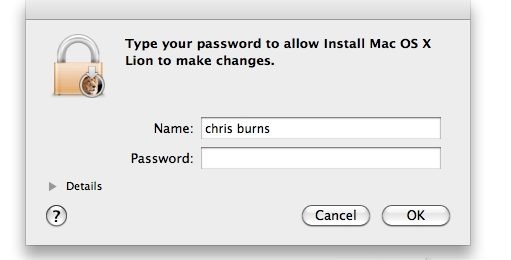
It appears that even requiring users to implement hard-to-hack password requirements doesn't prevent them from being as generic as possible. In a study of more than 2 million systems, Trustwave found that, not surprisingly, the most common password was "password," or some variation thereof. And among systems that required an upper-case letter and a number, Password1 was the top choice.
The study was released to highlight one of the most glaring problems with cyber security today – it doesn't matter how many firewalls or hacking-protective methods you put into place if someone is able to actually log in with verified credentials. The company noted that out of the 2.5 million passwords it looked at, 5% contained some form of the word "password," which makes it easily guessable by an automated password cracking software, or even an actual human being.
In fact, with only a $1,500 computer and a specialized program, Trustwave was able to mine 200,000 verified passwords from its pool of millions. Security experts say users need to use much more un-guessable passwords, but that's something they've been saying for years. They are increasingly saying that biometric (e.g., fingerprint) authentication or some other verification method that revolves around more than human memory is the only way to solve this problem.
[via CNN]