Malicious Google Play Store Apps Snoop On SMS To Make Purchases
Android malware isn't exactly new but you might presume they only come from apps downloaded from some shady sources. Anyone following mobile news, however, will probably be aware of how apps on the Google Play Store may turn out to be carriers for such malicious software, sometimes taking weeks or even months before someone discovers them. Such is the case with another batch of such malware-laden apps on Google's officially sanctioned and recommended app store, ones that misuse existing features to make unauthorized purchases.
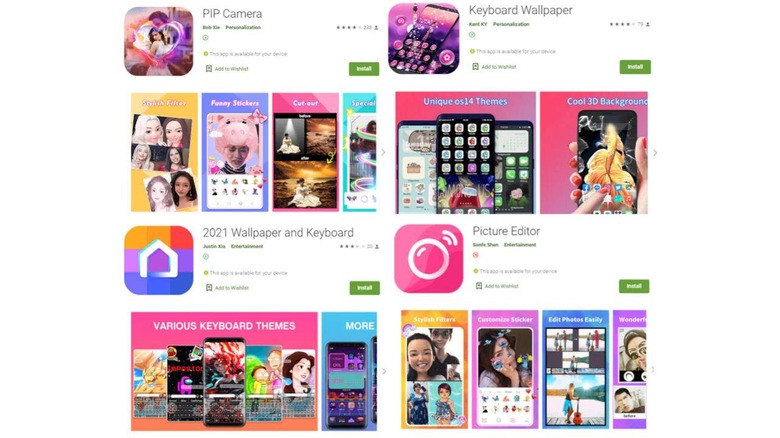
The way these apps have gotten past Google Play Store's security is almost genius in its simplicity. The authors upload clean versions of these apps as legit tools like photo editors, wallpaper apps, or puzzle games in order to get approval. Once in, the hackers then push an update that introduces the actual malicious code, which apparently doesn't get screened as strictly as the initial app was.
The way these malicious apps work is also quite interesting. Knowing that certain purchases require a one-tip PIN sent via SMS, the apps listen for such messages by hooking into Android's Notification Listener. That way, they won't need to ask permission to read SMS data, something that would have raised red flags.
The apps have already been rated terribly by those unlucky enough to have actually installed them. In addition to not working as advertised, users have reported unauthorized purchases made on their phones that were traced to these malicious apps. McAfee said it is working with Google to get these apps off the Play Store.
The malware isn't sophisticated enough to escape detection by McAfee's tools so the cybersecurity company recommends scanning your phone for this Android/Etinu threat. The malicious apps are reportedly targeting users in Southwest Asia and the Arabian Peninsula but McAfee worries that abuses of this Notification Listener functionality aren't going away anytime soon.