Linux C Library Exploit Affects All Systems Dating Back 2000
Sometimes, the price of popularity is more scrutiny. As the Linux operating system, and open source in general, gets more and more coverage in mainstream media and news, a lot of security holes, and big ones at that, are being exposed, or at the very least sensationalized. After the "Shellshock" bug last September, which was reported to be even worse than the "Heartbleed" bug of the open source OpenSSL vulnerability, comes a "GHOST" security exploit that affects almost all Linux systems that date all the way back to 2000.
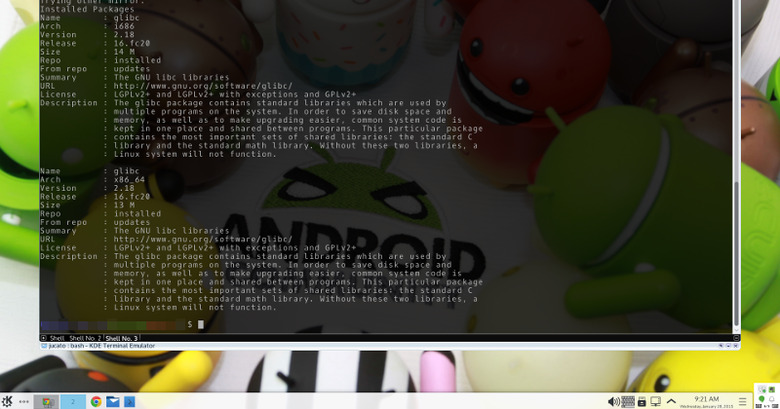
The bug, detailed in Qualys' security advisory CVE-2015-0235, is found in the GNU glibc software, the C library that underpins all Linux systems and is used by many software, so its effects are far-reaching. It affects a certain function named "__nss_hostname_digits_dots()" that, in turn, is used by the function "_gethostbyname()", hence the nickname "GHOST". Like many security holes of its kind, this one can cause a buffer overflow that would allow hackers to execute arbitrary code. According to Qualys, this exploit has been in existence since glibc version 2.2, which was released November 2000.
There are a few mitigating circumstances that makes GHOST less severe and worrying than, say, Shellshock. For one, the gethostbyname function itself is rarely used by more recent software and are made obsolete by IPv6. More importantly, the hole has been patched in a fix included between glibc 2.17 and glibc 2.18 in 2013. That means that many modern Linux distributions probably already have this fixed.
The problem is that the bug patch back then wasn't labeled as a security threat so some older Linux distributions, particularly those with long-term support, didn't apply that fix yet. These include distributions like Red Hat Enterprise Linux 6 & 7, CentOS 6 & 7, SUSE Linux Enterprise 11 and older, and Ubuntu 12.04. These happen to be just the kind of Linux distributions used more on servers and workstations in contrast to end-user desktops. Thus, there is even more urgency to get it fixed.
The good news is that, being open source software, the fixes and patches will be rolling out swiftly. Red Hat has already issued a fix for an even older Red Hat 5, while Novell announced that SUSE 12 and openSUSE 13.1 and 13.2 are not affected. And users of these distributions need not even have to wait for distributors to send out the patches, unlike other operating systems. They can fix things on their end interim, which is what many Linux system administrators do anyway.
SOURCE: Qualys
VIA: Threatpost