LightsOut Adware Infects Utility Apps, Bypasses Google Play Store Checks
Utility apps are a dime a dozen in Google Play Store, but if you're not careful, you might install one that has some unwanted payload inside. That is the unfortunate situation that a few million Android users may have found themselves in after downloading and installing some random flashlight or utility app, which left them exposed to ads in inappropriate places. And their only fault is to have presumed that since the apps are from Google Play Store, they must be safe to install and use.
Cyber security outfit Check Point disclosed the rather worrying situation. While the apps have already been taken down when Google was notified of their existence, the carrier apps have, which consisted of 22 flashlight and utility apps, have already been downloaded a total of 1.5 million to 7.5 million times.
"LightsOut", as Check Point called the hidden malware, is perhaps one of the most abusive kind of adware that has plagued Google Play Store. While it did not delete critical files, it did pop up at inappropriate or unrelated times, like when making a phone call. This forced users to tap an ad to perform even basic tasks which, of course, generated revenue for cyber criminals.
Almost like the homicidal AI of science fiction, LightsOut has some self-preservation features. Since the ads pop up outside of the flashlight or utility app, the user has no way of knowing they come from those. It can even hide the app icon to make uninstalling the app even harder.
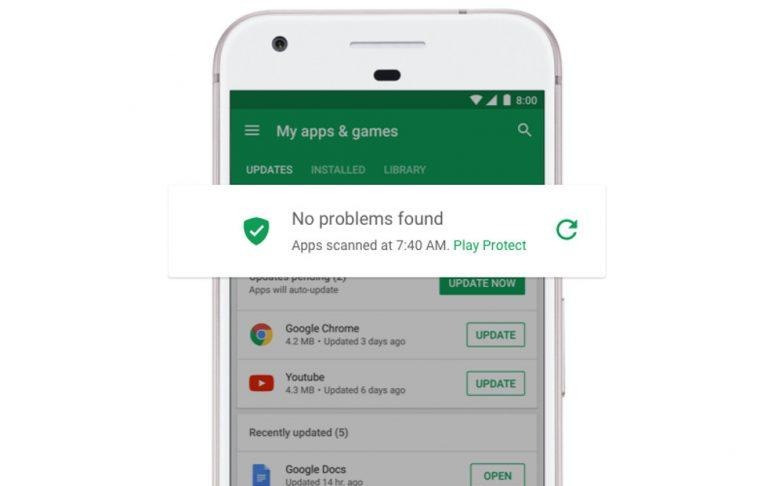
Perhaps the most worrying part of LightsOut's stint in Google Play Store is that it got there at all, undetected even. Google loves to talk about how its machine learning and algorithms are able to automate security checks, removing the need for manual screening of apps. Unfortunately, instances like these, however small, corrode any confidence in the effectiveness of that method until people will hold suspect any and all apps that come even from Google Play Store.