HummingBad malware puts 10 million Android devices at risk
There are some malware that are just plain horrifying, like the past Stagefright exploit. Some, like weak ransomware, are a nuisance at best. HummingBad, reported by security outfit Check Point, sits precariously in the middle. Right now, all it does is to compromise an Android device in order to trick people into clicking on ads in order to generate revenue for its creators and its partners. It has, however, the potential to do even more destructive, and profitable, things should the people behind it decide to go beyond mere money-making into a full-on war against security.
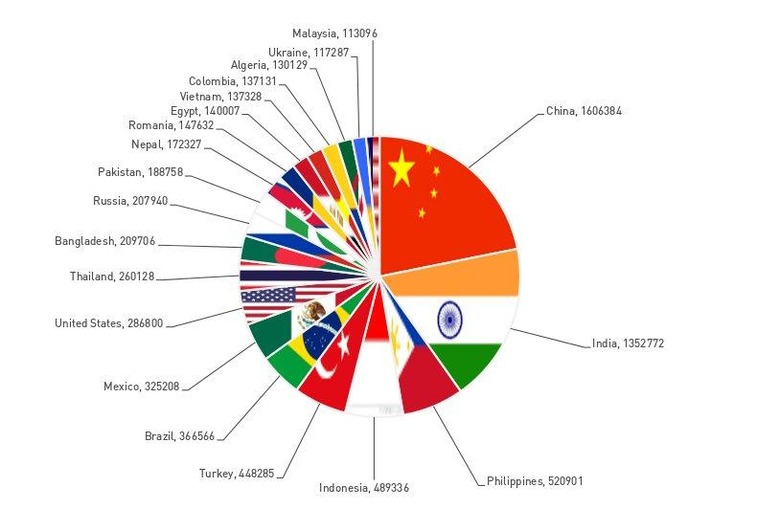
This isn't to downplay the effects and reach of HummingBad. According to Check Point, as much as 10 million devices around the globe have infected apps installed on their Android smartphone or tablet. Unsurprisingly, majority of those come from China, India, and the usual Asian countries, but the US isn't clean of it either.
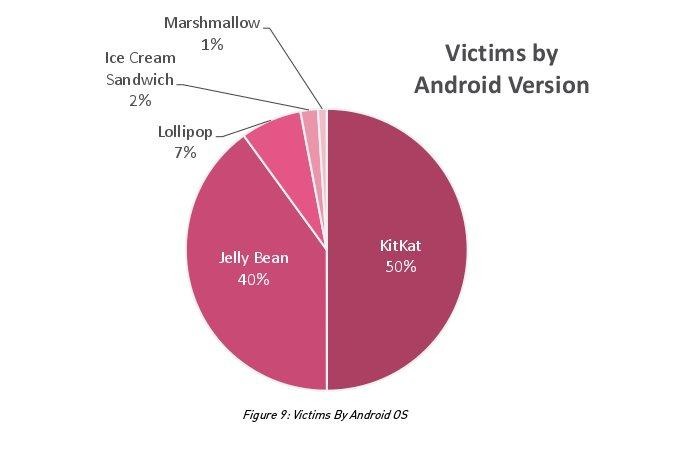
At the moment, however, HummingBad isn't doing maximum damage. It does attempt to root devices in order to further spread its malware, install more infected apps, and whatnot. Failing to do that, it has fallback measures to gain access. All of these are being done in the name of generating ad revenue. However, considering it tries to gain root access, its actual potential is far more frightening. That said, based on Check Point's own data, older Android devices are more prone to getting infected, with Android 5.0 Lollipop and Android 6.0 Marshmallow showing the smallest shares.
However, it is the narrative around HummingBad that is actually more worrying. Check Point traced the malware to a Chinese entity named YingMob, which turned out to be a mobile ad server company. In a nutshell, it is actually a legit company partnering with other legit companies to serve ads. Most malware groups turn to hide underground, but YingMob operates out in the open, though the group behind HummingBad is just one part of the company. For now, it is perhaps in YingMob's best interests to keep its effects on infected devices low-key, as they can generate more ad clicks that way. But if they do decide to flip the switch, HummingBad could have access to almost any information stored on a device given how it uses root access to its dirty work.
Sadly, Check Point hasn't revealed how to fix or even detect HummingBad infected devices. At the moment, prevention remains the best cure, which isn't that hard to accomplish given these rather simple steps.
SOURCE: Check Point (PDF)
