Google's "war against account hijackers" results in a 99.7% reduction
We've all heard about the travel money scam – a friend contacts you via IM or email frantic, saying they are overseas and have lost all their money and need some to get help. Many other variations exist, as well as other scams altogether. The hijacking attempts reached their peek in the summer of 2011, prompting Google to declare a "war against account hijackers." Earlier today, the company announced that Google account hacking has been reduced by 99.7-percent since then.
Initially, spammers were forced to change how they went about scamming individuals due to security measures implemented with the accounts. To get around them, the scammers were forced to hijack email accounts, as well as any other account they can get into using the same login information. According to Google, it has observed individual hijackers attempting to infiltrate a million Gmail accounts for weeks on end using stolen passwords.
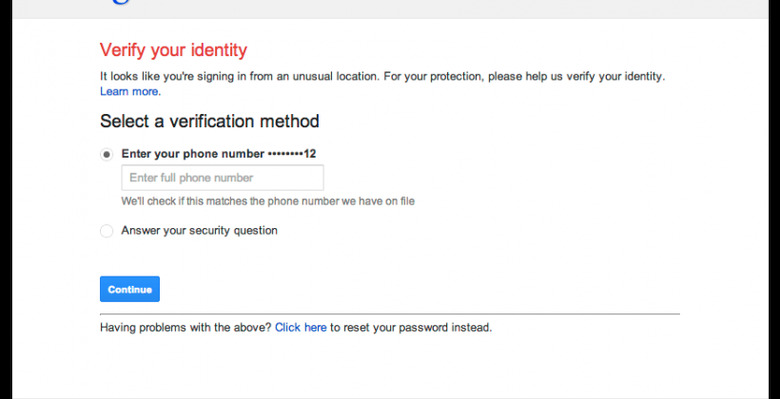
To help protect against these issues, Google implemented security measures that looked beyond the simple email/password combination. A series of variables are looked at when checking whether the account is being accessed by its owner; there are in excess of 120 variables that can be used. If the login looks too risky, other security measures are kicked into gear.
Questions are posed to the person logging into the account, such as the phone number associated with it or the security question that was created when the account was made. As Google states, because of the nature of these questions, it is difficult for a hijacker who has the email/password combo to know these answers. As a result, Google has seen a drop in account hijacking of 99.7-percent since 2011.
Still, as Google points out, the best security involves help from the account owner. Gmail users can help foil attackers by using a complex, unique password, by turning on 2-step verification, and by ensuring that the recovery options in the account are set up with correct information, such as a secondary email address and phone number.
[via Google Public Policy Blogspot]