Google's Password Alert already patched but still vulnerable
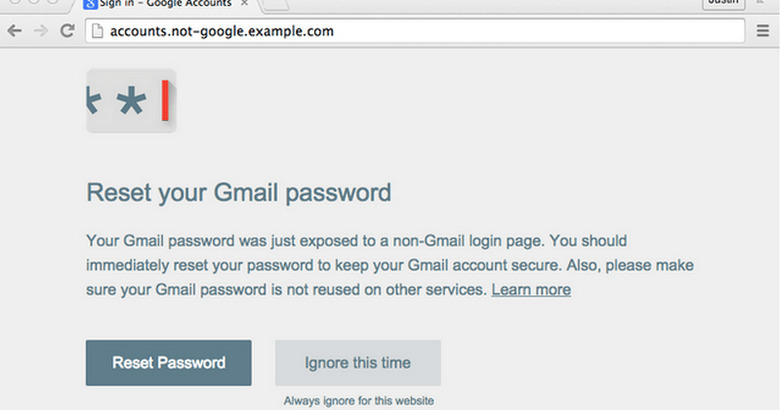
Earlier this week, Google released a Chrome extension designed to protect against phishing attacks, particularly the kind that directs users to a page designed to look like one of Google's own login pages. When on one of these fake Google logins, the Password Alert extension was designed to identify that it was a phishing attempt and alert the user that they were about to enter their credentials on a Web page that isn't part of Google. The problem is that the extension itself was vulnerable, and remains that way despite a patch.
An information security consultant named Paul Moore was the first to spot a vulnerability in the fresh Chrome extension, revealing that a Web page needed to add only seven lines of code to foil Password Alert, something he called "an embarrassment".
A security engineer with Google responded to Moore's tweet about it with a tweet of his own, saying the extension had been updated to patch the vulnerability. Those who had it needed (and still should) update to the newest version.
The problem, for Google at least, is that Moore took a look at the newest version (1.4) and announced on his Twitter that he'd managed to bypass it again, despite the patch. Google hasn't yet responded to this revelation, however.
SOURCE: CNET