Google and Massachusetts accused of silently installing COVID-19 app
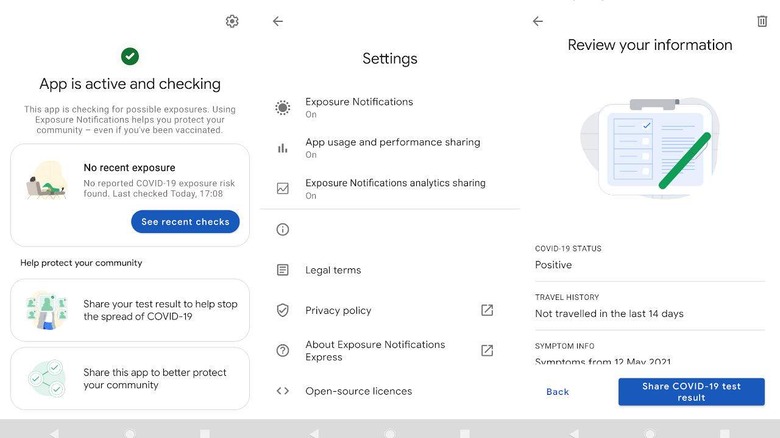
COVID-19 tracking apps have always been a sensitive topic since the concept came up last year. While such apps made it convenient and easy to do contract tracing and exposure notification, they also made it almost too easy to have privacy violations from third parties, companies, or even governments. Google and Apple providing official frameworks for authorized apps to hook into only offered some amount of comfort and assurance, but, it turns out, it might not be completely worry-free. A growing number of reports try to demonstrate how Google and the government of Massachusetts worked silently behind the scenes to install the latter's MassNotify Android app on users that haven't even agreed to Android's official Exposure Notification feature.
The basic idea behind COVID-19 contact tracing apps is to have a location-aware device that you have on you all the time. While some versions make use of QR codes or even manual input, the most convenient implementations are able to log where you've been and, if someone in the same area tested positive for the virus, you would also be immediately informed. That alone raises many privacy red flags that proponents have tried to address in many ways.
One of those ways is to have official APIs made and authorized by Google and Apple only for such purposes on Android and iOS, respectively. The platform makers would then screen and vet apps that make use of such apps, usually ones that come from government agencies or accredited health organizations. In other words, it is only with Google's or Apple's knowledge and approval that such apps can be installed, making this incident in Massachusetts all the more complicated.
People are now reporting that this MassNotify app suddenly got installed without their knowledge, let alone their approval. They only became aware of the fact when they got notifications from the that they had no idea was even installed. They also couldn't easily uninstall the app because it doesn't exactly get listed in the usual places for Android apps.
MassNotify's Help Desk admits that the app is installed but isn't enabled. Google confirms this setup, explaining that the functionality is built into a device's settings but only gets enabled if they explicitly turn on Exposure Notifications. The fact that Google and a government-sanction app developer were able to install an app behind their backs is likely to unsettle many Android users, especially when that app can become a liability, unintentionally or otherwise.