GCHQ Hacked GRX And OPEC Employees Via Quantum Inserts, Snowden Papers Show
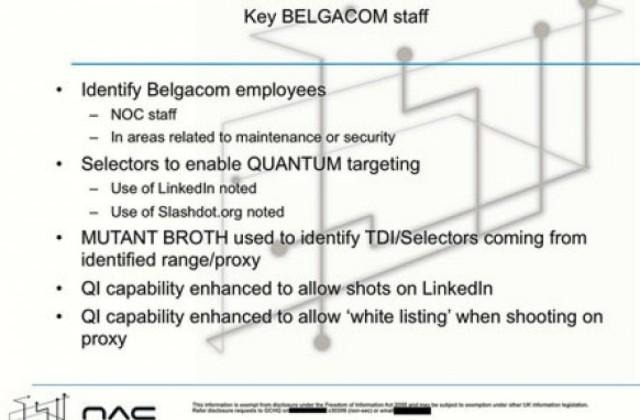
A new analysis of the Snowden papers by German magazine Der Spiegel shows GCHQ–the English counterpart to the US's NSA–served false copies of LinkedIn and Slashdot pages to install malware on a few target individuals' computers. This latest revelation is not a mass spying program, but a server-heavy, speed-dependent initiative to spy on key individuals deemed to be assets by the GCHQ. Targets included employees of GRX providers Comfon, Mach (now owned by Syniverse), and nine members of OPEC, the global oil cartel.
The so-called "Quantum insert" was also used on Belgian GRX provider BICS as reported a few weeks ago. The technique is an aspect of a larger strategy used by the GCHQ as well as the NSA to place a system of "secret servers, codenamed Quantum, at key places on the Internet backbone," according to cryptographer and security expert Bruce Schneier. Ars Technica highlights an excerpt from a post on Schneier's blog from last month:
"This placement ensures that they can react faster than other websites can. By exploiting that speed difference, these servers can impersonate a visited website to the target before the legitimate website can respond, thereby tricking the target's browser to visit a Foxacid (sic) server."
FoxAcid is a system of secret NSA servers used for hacking and spying on Internet-connected computers. It's unclear whether the GCHQ has its own version of FoxAcid or whether it just piggybacks on the NSA's servers as per their unique surveillance cooperation relationship. Schneier further explains:
"They (Quantum inserts) are hard for any organization other than the NSA to reliably execute, because they require the attacker to have a privileged position on the Internet backbone and exploit a 'race condition' between the NSA server and the legitimate website."
Quantum, in turn, is part of a larger NSA spying program called Turmoil. The GCHQ Quantum inserts are notable in that rely on servers faster–and more strategically placed–than the popular websites they impersonate. Speed is of the essence. Only a highly funded, extremely powerful body such as a governmental spy agency can pull it off. The reason the GCHQ targeted employees of GRX providers is that GRXs (Global Roaming Exchanges) handle an incredible amount of global Internet traffic; only about two dozen GRXs exist. They therefore represent an efficient application of institutional resources. If spy agencies can get a hold of key GRX provider employees' computers, they can use that as leverage (presumably through some combination of silent surveillance, compensation, or blackmail) into the larger GRX infrastructure for more spying.
The upshot of all this is that the GCHQ used Quantum hack-and-spy techniques to pave the way for more hacking and spying. In other words, the Quantum inserts described in this latest analysis of the Snowden papers are part of a larger program to build a digital panopticon. As far as why spy agencies would target members of OPEC, that's more in the realm of classical cloak-and-dagger practices: oil-producing nations simply have geopolitical power, and so they've long been considered fair game in the anarchical global order.
SOURCE: Der Spiegel (German)
Via: Ars Technica