Foscam IP Camera Bug Lets Anyone View And Record Live Footage
One of the most important uses of IP cameras is for remotely viewing places or people for safety and security purposes. But in a rather ironic turn of events, a number of Foscam IP cameras have been discovered to be easily compromised, giving anyone with an Internet connection access to what the camera is seeing as well.
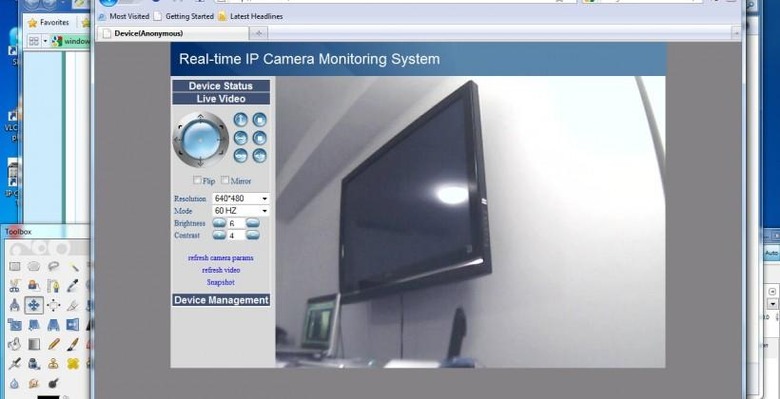
According to a thread in Foscam's support forum, the bug exists in the camera's firmware and can be accessed through the Web interface. Any user, authorized or not, can view the camera's live video feed by simply pressing OK when asked for a user name and password, making such security measures totally useless. This practically turns a camera used for security into one that's can be used for spying or other nefarious purposes.
To be fair, not all cameras from the Chinese manufacturer are affected. The bug can only be found on MJPEG cameras and only those on the .54 firmware version. Aside from a specific number of models, no other vulnerabilities similar to this are currently known for other Foscam cameras.
However, this is not the first vulnerability that Foscam experienced. And unfortunately, this incident is just the latest in a series of unchecked security holes in IP cameras. A slightly similar bug existed in some TRENDnet cameras that allowed outsiders to snoop in. Vulnerabilities like this do require third parties to know the IP address of the camera they want to target, but there are existing search engines that can actually make this quite easy.
Foscam said that it will be rolling out firmware version .55 soon to plug the security hole. In the meantime, there is also a workaround available for users to try out while waiting for Foscam to make their move.
VIA: Krebs on Security